
Image: Shutterstock/LeoWolfert
One great thing about Linux and the open source community is that as soon as a vulnerability is detected, developers are hard at work releasing tools to mitigate the problem. Such is the case with the Log4j vulnerability.
This particular issue is quite bad, as it affects so many servers and projects. Here’s how the Log4j vulnerability works:
- Log4j2 supports a logging feature called Message Lookup Substitution, which enables special strings to be replaced, during the time of logging, by other dynamically generated strings.
- One of the lookup methods (JNDI paired with LDAP) fetches a special class from a remote source to deserialize it, which executes some of the class code.
- Any part of the logged string can then be controlled by a remote attacker.
Part of the problem is that Log4j is so deeply embedded in Java projects and dependencies that are used by quite a lot of tools. So finding every vulnerability in your server can be tricky.
Fortunately, plenty of efforts have been taken to help locate these issues. One such effort is Log4j Detect, which will scan your development projects to ensure they’re free from vulnerabilities.
I want to show you how to use the Log4j Detect script to scan your Java projects.
What you’ll need
To work with this script, you’ll need a Java project and a user with sudo privileges. That’s it. Let’s get to work. This script can be used on Linux, macOS and Windows. I’ll be demonstrating on Linux (via Ubuntu Server 20.04).
SEE: Log4j: How to protect yourself from this security vulnerability (TechRepublic)
How to download and install Log4j Detect
The first thing to be done is the installation of Log4j Detect. To do that, log into your Linux server and download the script by first setting your system architecture as an environment variable with:
ARCH=amd64
If your architecture is ARM, that command would be:
ARCH=arm64
Next, download the script with:
wget "https://github.com/whitesource/log4j-detect-distribution/releases/latest/download/log4j-detect-1.3.0-darwin-$ARCH.tar.gz"
Unpack the file with:
tar -xzvf log4j-detect-1.3.0-darwin-$ARCH.tar.gz
Give the file the proper permissions with:
chmod +x log4j-detect
Move the file into /usr/local/bin with:
sudo mv log4j-detect /usr/local/bin/
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
How to scan your project with Log4j-detect
Now that the installation is complete, let’s scan a project for Log4j vulnerabilities. Let’s say your project is housed in a directory named JAVAWeb-Project. Change into that directory and issue the command:
log4j-detect scan
Depending on how large your project is, the scan shouldn’t take too long to complete. When it does, it’ll report back if there are any issues (Figure A).
Figure A
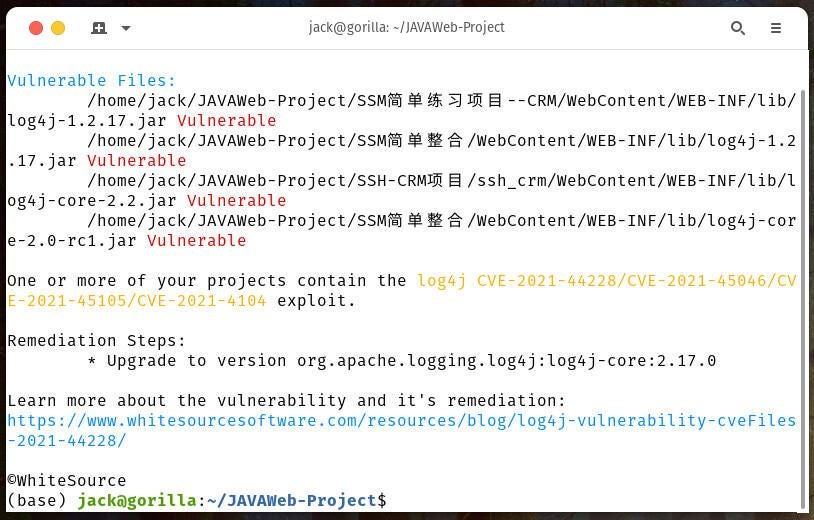
As you can see, the Java project I tested has Log4j issues that must be addressed. The script will point out the problems as well as how to remediate the issue. Once you’ve addressed everything, run the script again to see if the vulnerabilities are no longer detected.
You should consider this a must-do for every project and server you suspect could be vulnerable to Log4j (and even those you might think are safe). This is one case where you are most certainly better safe than sorry.
Subscribe to TechRepublic’s How To Make Tech Work on YouTube for all the latest tech advice for business pros from Jack Wallen.
