
Researchers from Avanan, a Check Point company, have announced the discovery of attacks exploiting the Microsoft Teams communication platform to infect corporate users.
How the attacks got their initial foothold
Microsoft Teams is a popular platform adopted by many companies worldwide, part of the Microsoft 365 family of products. This platform allows its users to do audio and video conferencing, chat in multiple channels and exchange files between users and groups of users.
From a cyberespionage perspective, it sounds like a goldmine, since getting access to the Teams platform of a targeted company would mean getting access to all conversations from the different channels, which might contain very sensitive information or intellectual property. It also might contain sensitive files shared between its users. Yet it is also interesting for financially motivated cybercriminals, since they might just be able to catch interesting data inside Teams, which might allow them to commit more fraud, like obtaining credit card information for example.
To achieve accessing the Teams platform, the only thing the attacker needs is valid credentials from one of the employees of the targeted entity. As mentioned by Avanan, this might be done by obtaining the e-mail credentials of any user, which is often done by running phishing campaigns.
Of course, attackers might also just buy valid credentials from initial access brokers or use social engineering to target a particular user and manage to get his or her corporate password.
Infection via Teams
Once an attacker has obtained a valid e-mail credential, he or she is able to log into the Teams platform of the company.
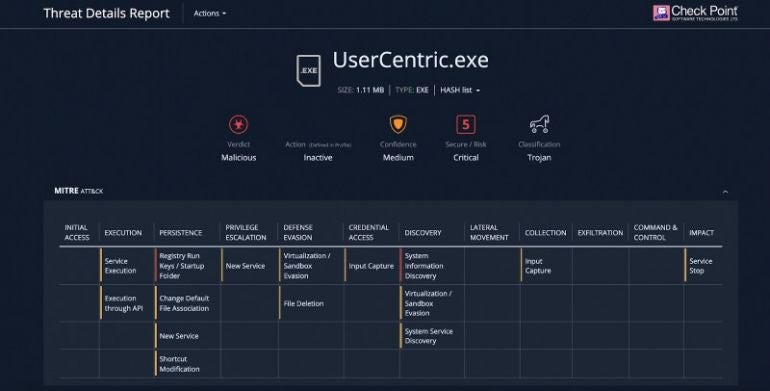
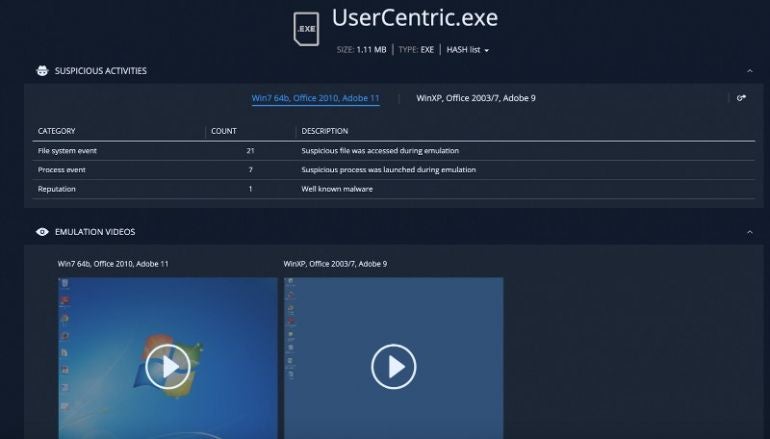
This is where Avanan has seen thousands attacks per month. The attacker operates by dropping executable (.exe) files named “UserCentric.exe” into different Teams conversations, the executable being a malicious file, generally a trojan. The file writes data to the Windows registry, installs DLL files and creates shortcut links that allow the program to self-administer and take control over the computers.
Avanan did not mention the ultimate goal for infecting users with this malware, but we can suspect it’s to allow attackers to get more data from the internal network of their target or get full access to computers within the network. This knowledge might in turn be used for financial fraud or cyberespionage.
A perfect target?
Microsoft Teams does not have a malicious link detection system, and it only has a common virus detection engine. Users, since they connect to a platform provided by their companies, tend to systematically trust everything that is shared on it, in a false feeling of “everything is secure here.”
That trust entices users to share much more data than they usually would on a platform that they are not familiar with, from a security point of view.
Not only can attackers put infecting links or direct files on the different chat channels, but they might also chat in private with any user and use social engineering skills to infect them.
Very few users will care to save the obtained files on their hard drives and launch antivirus or threat detection products on it before opening them.
Seeing thousands of such attacks, Avanan said it expects a significant increase in these sorts of attacks in the future.
How to protect yourself from a Teams attack
For starters, everything must of course be done to protect every user’s email credentials.
In addition, here is what should be done by IT regarding the specific Teams threat reported in this article:
- Enable two-factor authentication on the Microsoft accounts used for Teams so that users need to use a validation on their phones.
- Implement additional security for every file that is dropped on the SharePoint folders related to Teams. Files should all be checked against a threat detection solution. Their cryptographic hashes could also be submitted to VirusTotal in order to check if the file might already be known and classified as malicious or not.
- Implement additional security for every link that is copied on Teams. If possible, use several link reputation services to check if the link is safe or not.
- Raise awareness among employees. In the same way awareness is raised for phishing attacks and all email threats, employees should be told about the risks of communication and sharing platforms.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.


