
The cyberthreat landscape is constantly evolving, with new attacks developing every day. In their new report, SonicWall explores some of the most dangerous trends that security professionals need to have on their radar.
SEE: How to develop competency in cyber threat intelligence capabilities (TechRepublic)
Ever-changing global malware activity
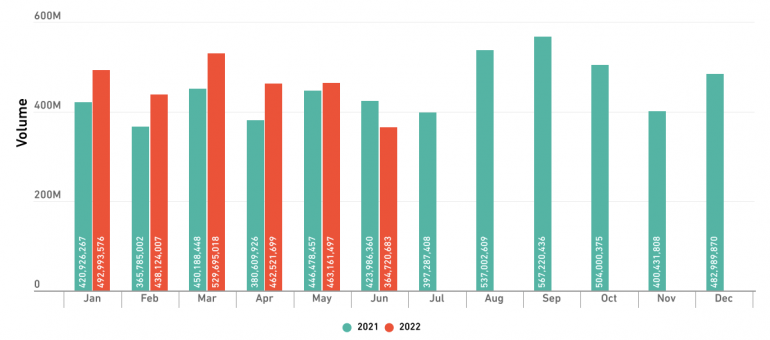
SonicWall Capture Labs threat researchers recorded 2.8 billion malware hits, in the first half of 2022. Except for June, the global malware detection has been higher in 2022 when compared to 2021 (Figure A).
Figure A
The malware categories that have been increasing the most are cryptojacking malware (30% increase) and Internet of Things-related malware (77% increase).
Some changes in regional data have also been reported. Attacks on North America increased by 2%, which is much lower than the global average. Yet, Europe has shown a 29% increase in cyberattacks, and attacks in Asia grew by 32%.
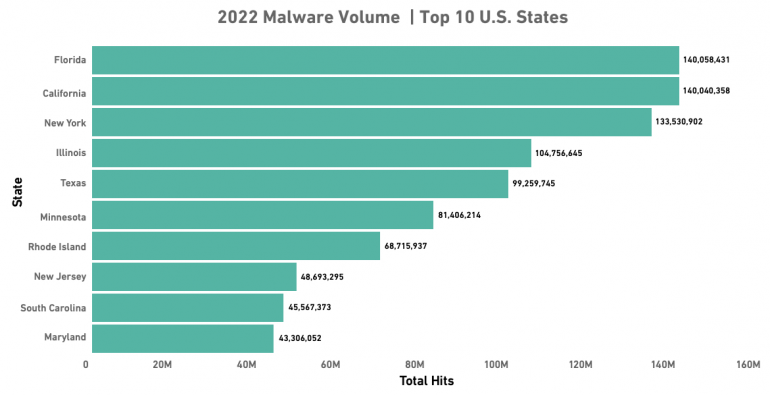
Regarding the U.S. states affected, Florida is still the most hit state, followed by California and New York (Figure B).
Figure B
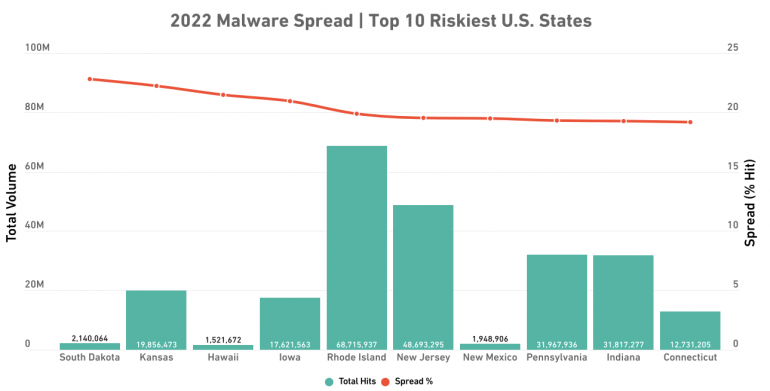
Yet another indicator needs to be considered: The malware spread percentage, which takes into consideration not only the volume of detected malware, but also the number of sensors detecting that activity for a region.
Once calculated, the malware spread indicates that South Dakota is the riskiest area for organizations, followed by Kansas and Hawaii (Figure C). Texas, on the other hand, is the safest state. Although it has 99.3 million malware detected, it only represents 15.5% of organizations seeing attempted malware attacks.
Figure C
As for the different industries being hit by malware, education is the most targeted, with an increase of 21.4% per month, followed by the government at 19.3%. Financial institutions have been less targeted with only 15.2% of financial organizations being hit by malware.
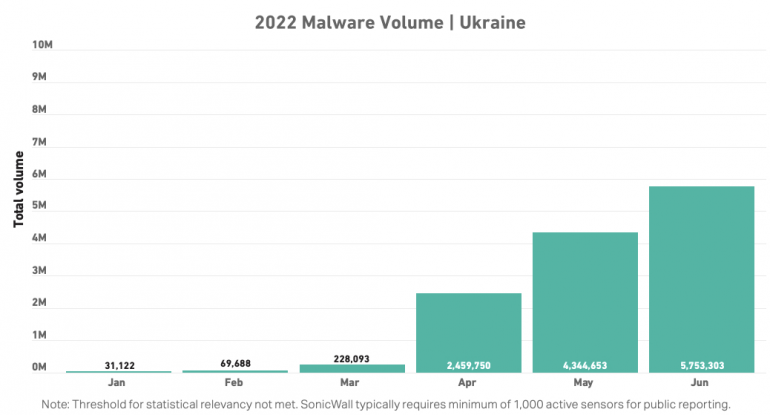
On a side note, SonicWall, although not having enough sensors in Ukraine to meet statistical relevance, took an interest in checking malware hits in that country, and saw an extraordinary increase in malware starting in March 2022 (Figure D).
Figure D
The ransomware situation
Ransomware attacks have been going down by 23%, with 236.1 million ransomware attempts reported in the first half of 2022 (Figure E). The three most used ransomware families are Cerber, Ryuk and Gandcrab. The latter was shut down in 2019, but as it was provided as a service, those numbers probably reflect old campaigns.
Figure E
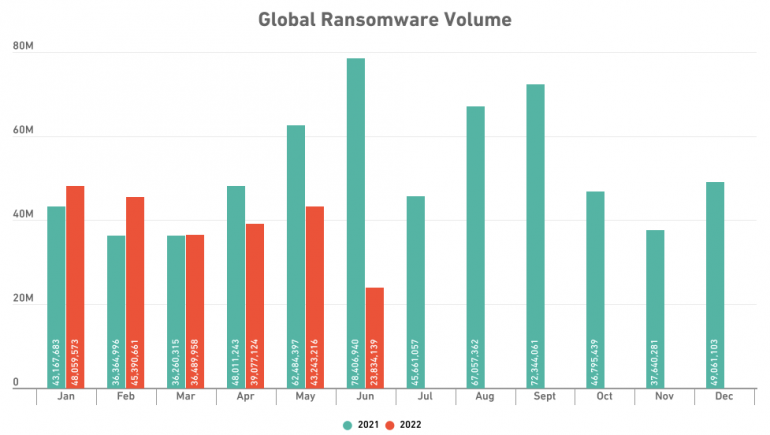
After two years of increase, the global number of ransomware detections started steadily decreasing from Q3 2021. While it is good news, the amount seen in the first half of 2022 is still higher than the full-year totals for each of 2017, 2018 and 2019, according to the researchers.
The United States is still the most impacted country in 2022 (Figure F).
Figure F
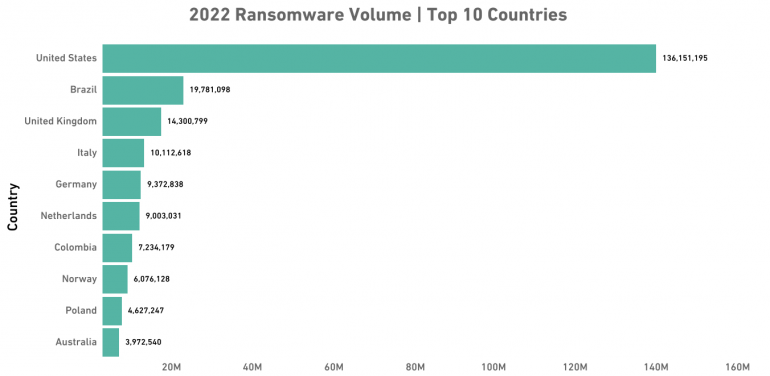
European countries are increasingly appearing in the top 11, with seven countries as opposed to only five in 2021.
Several factors might explain the drop in ransomware attacks. An increased hardening of organizations, continued volatility of cryptocurrency prices, more stringent regulations from cybersecurity insurance underwriters might all be factors, according to the researchers.
Yet, the NSA says the biggest factor is likely to be political conflicts and the fact that Russians are more focused on activities related to Ukraine. Those cyber criminals also have more trouble using credit cards and other ways to purchase infrastructure in Western countries and suffer from increasing difficulties to move money.
IoT malware increases
IoT malware has increased by 77% year to date, even exceeding as much as 12 million detections between January and June 2022 (Figure G).
Figure G
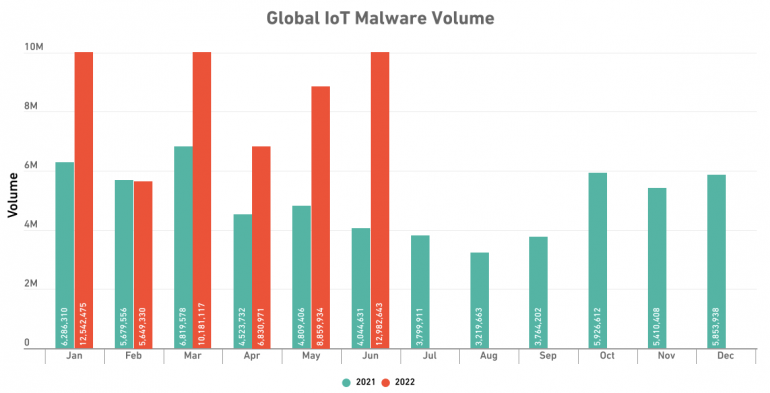
North America saw more than 5 million detections for the first time ever in January 2022, reaching 6.7 million. In June, it even reached 8.1 million. Detections in Asia increased by 74%, reaching 2 million in January, while in Europe, they decreased by 19%.
As for the industries targeted, every industry showed triple-digit attack volume increases. Finance grew by 151%, healthcare by 123%, retail by 122%, government by 114% and education by 110%.
Cryptojacking trends
Global cryptojacking reached 66.7 million hits in the first half of 2022, which represents a 30% increase compared to the first half of 2021. The three most targeted industries — government, healthcare and education — dropped 78%, 87% and 96% respectively, while retail increased 63% year to date, and finance increased 269%.
Although cryptomoney is unstable and Bitcoin dropped a lot since 2021, it is still easier for cyber criminals to dig harder than to find a new way to make money, which explains the increase in cryptojacking attacks.
According to the researchers, some ransomware operators are also changing activity to cryptojacking. While it brings less money than ransomware, it is much quieter in terms of detection, and some cryptojacking victims are never aware of it, resulting in lower risks that attracts some cyber criminals.
More threats
Malicious PDF and Microsoft Office files are on the rise, with Excel still being the most exploited Microsoft Office application. Attackers mostly abuse the XLM (Excel Macro 4.0) macro code, whereas before, they exploited Visual Basic Analysis macros. Most recently, attackers started to use a combination of XML and VBA to perform malicious activities.
Log4j vulnerability exploitation is still high, with an average of 2.8 million exploit attempts every day.
Encrypted attacks—attacks driven using encrypted communication—have seen a 132% increase from January to July 2022, mostly targeting government, finance and education.
Intrusion attempts rose 18% in the first half of 2022, while malicious intrusions (i.e., attempts of medium to high severity) dropped 19% for the same period in 2021.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

