
Threat actors have been exploiting a NetScaler appliance vulnerability to get persistent access to the compromised systems. Find out which NetScaler systems are affected, how attackers are hitting vulnerable systems worldwide and how to protect your business from this cybersecurity attack.
Jump to:
- Exploited Citrix NetScaler vulnerability
- Exposed NetScaler appliances backdoored with web shells
- Successful exploitation may lead to more than just planting web shells
- How to protect your business from this cybersecurity threat
Exploited Citrix NetScaler vulnerability
Citrix published a security bulletin on July 18, 2023 about three vulnerabilities in NetScaler ADC and NetScaler Gateway: CVE-2023-3519, CVE-2023-3466 and CVE-2023-3467. This bulletin detailed exploits on CVE-2023-3519 observed in the wild on unmitigated appliances. Affected systems are:
- NetScaler ADC and NetScaler Gateway 13.1-49.13 and later, 13.0-91.13 and later.
- NetScaler ADC 13.1-FIPS 12.1-37.159 and later.
- NetScaler ADC 12.1-FIPS 12.1-55.297 and later.
- NetScaler ADC 12.1-NDcPP 12.1-55.297 and later.
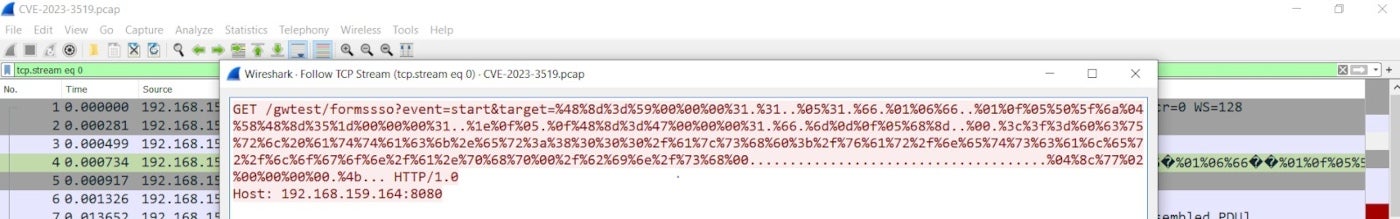
ZScaler, a cloud security company, provided more details on how the NetScaler vulnerability can be triggered and allow an unauthenticated attacker to execute arbitrary code as the root user. A specially crafted HTTP GET request can be used to trigger a stack buffer overflow in the NetScaler Packet Processing Engine, which runs as root (Figure A). A proof of concept is available on GitHub.
Figure A
Exposed NetScaler appliances backdoored with web shells
Fox-IT, part of the information assurance firm NCC Group based in the U.K., responded to several incidents related to the vulnerability in July and August 2023, with several web shells found during the investigations. This is consistent with other reports such as the one from the nonprofit organization Shadowserver Foundation and trusted partners making the internet more secure.
Following those discoveries, Fox-IT scanned accessible NetScalers on the internet for known web shell paths. The researchers found that approximately 2,000 unique IP addresses were probably backdoored with a webshell as of Aug. 9, 2023. Fox-IT’s discoveries were shared with the Dutch Institute for Vulnerability Disclosure, which notified administrators of the vulnerable systems.
SEE: Download TechRepublic Premium’s network and systems security checklist.
Shadowserver reported the U.S. is the country with the most unique IPs of unpatched systems, with more than 2,600 unique IPs being vulnerable to CVE-2023-3519 (Figure B).
Figure B

Fox-IT reported that approximately 69% of the NetScalers that currently contain a web shell backdoor are not vulnerable anymore to CVE-2023-3519; this means that, while most administrators have deployed the fixes, they have not carefully checked the systems for signs of successful exploitation and are still compromised. The company provides a map of compromised NetScaler appliances by country (Figure C).
Figure C
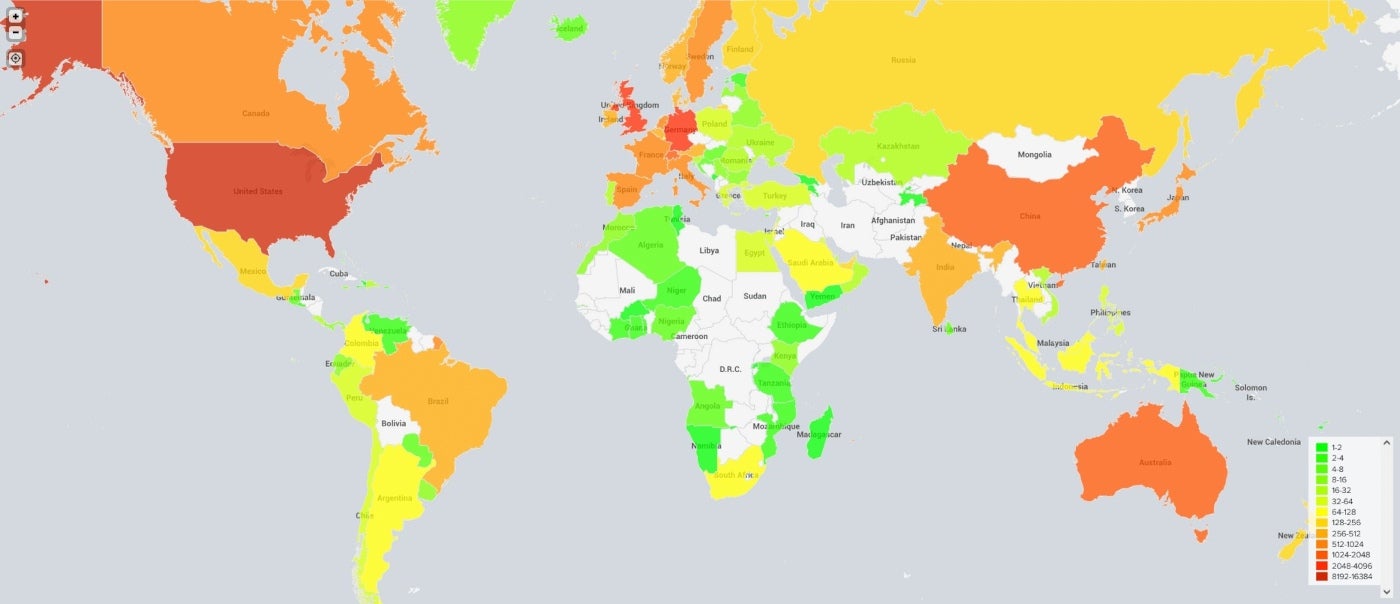
Most compromised NetScalers are located in Europe. Fox-IT researchers stated that “there are stark differences between countries in terms of what percentage of their NetScalers were compromised. For example, while Canada, Russia and the United States of America all had thousands of vulnerable NetScalers on July 21, virtually none of these NetScalers were found to have a webshell on them. As of now, we have no clear explanation for these differences, nor do we have a confident hypothesis to explain which NetScalers were targeted by the adversary and which ones were not.”
Successful exploitation may lead to more than just planting web shells
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
In addition, the Cybersecurity and Infrastructure Security Agency reported web shell implants exploiting CVE-2023-3519. The report noted that attackers exploited the vulnerability as early as June 2023 and used the web shell to extend their compromise and exfiltrate the Active Directory of a critical infrastructure organization. The threat actor managed to access NetScale configuration files and decryption keys and used the decrypted AD credential to query the AD and exfiltrate the collected data.
While this critical infrastructure used segmentation that did not allow attackers to move further with their attacks, it is possible that other organizations might be fully compromised by threat actors using the same methods.
Dave Mitchell, chief technical officer at cybersecurity company HYAS, stated that “unfortunately, this is far from the first time this has happened in recent memory. In previous campaigns, attackers gained footholds within F5, Fortinet and VMware appliances through exposed management interfaces in order to avoid detection by EDR software. Regardless if the exploit is already in the wild, customers are expected to monitor their devices for the IOCs before and after the patch is applied — which is obviously not at an acceptable level. The reason for this gap may be education, outsourced managed devices or division of security labor within an organization, but I do not expect attacks on network devices to stop anytime soon.”
How to protect your business from this cybersecurity threat
- Patch and update vulnerable Citrix NetScaler appliances now.
- Check for compromises in the affected systems because, if a threat actor has successfully compromised the system, the person might be able to access it even though the patch has been deployed. Shadowserver provided command lines to detect typical web shell components in web-exposed folders of the appliances, together with binaries with higher privileges. CISA provided command lines to check for files created after the last installation on the appliance.
- Analyze all HTTP log files carefully. Network log files such as DNS logs and AD/LDAP/LDAPS logs should be analyzed for any anomalies or traffic spikes.
- Deploy security solutions on all systems to try to detect potential malware resulting from the attack.
- Keep all appliances and systems up to date and patched with multifactor authentication enabled where possible to prevent attackers from exploiting common vulnerabilities and stolen credentials.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

