
Media organizations and journalists in the last years have been increasingly targeted by state-sponsored advanced persistent threat actors with a clear purpose: Obtain access to their sensitive information, spy their activities or even identify their sources. In addition, compromised journalist accounts might also be used for spreading disinformation or pro-state propaganda.
Email is the initial infection vector that is the most often used, but the threat actors also target social media accounts.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
A new publication from Proofpoint exposes several of these targeted attacks in an attempt to raise awareness.
Four state-sponsored campaigns against journalists
China’s TA412 and TA459
Zirconium, a threat actor also known as TA412, has been targeting American journalists since 2021. The actor, aligned with Chinese state interests, has often used emails to target people with web beacons before fully compromising them.
Web beacons, also known as tracking pixels, are invisible objects within an HTML-crafted email which discreetly retrieve a benign image file from an attacker-owned server. This way, the attacker can collect information about the visitor such as its external IP address, his user-agent and his email address to validate that the user account is active.
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
Beginning in 2021, TA412 launched at least five campaigns targeting American journalists covering U.S. politics and national security during events such as the attack on Jan. 6 of the Capitol.
In August 2021, the threat actor once again launched an attack campaign, this time targeting journalists with cybersecurity, surveillance and privacy issues focusing on China.
In 2022, the threat actor targeted journalists reporting on American and European engagement in the anticipated Russo-Ukrainian War.
Meanwhile, the threat actor TA459 targeted media employees with emails containing a malicious RTF attachment. Once opened, it would install and run a malware known as Chinoxy.
North Korea’s TA404
In early 2022, threat actor TA404, also known as Lazarus, created fake job offer pages designed to look like a branded job posting website in a campaign dubbed Operation Dream Job (Figure A).
Figure A
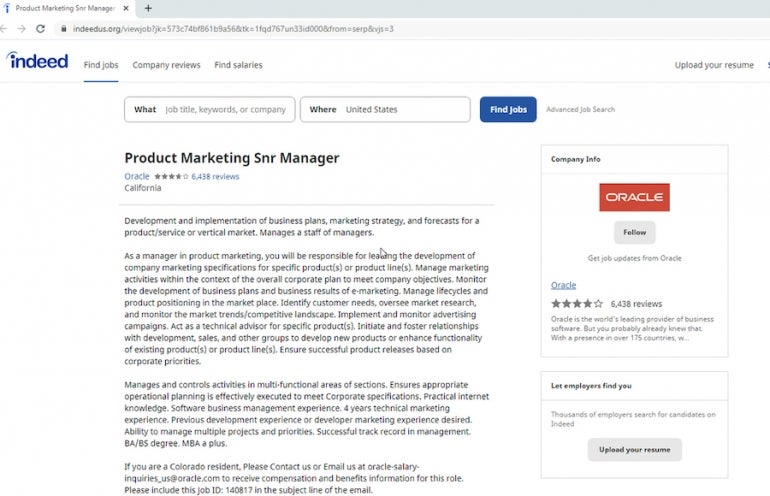
Links to these pages were sent to American targets belonging to a media organization which had published an article that was critical of North Korean leader Kim Jong-un.
An exploit kit would then compromise the visitors with malware and provide access to the compromised device.
Turkey’s TA482
TA482 is a threat actor targeting the social media accounts of American journalists and media organizations. According to Proofpoint, the threat actor aligns with Turkish state interests.
In early 2022, TA482 used social engineering to send an email supposedly from Twitter’s Security Center, warning the user of a suspicious connection (Figure B).
Figure B
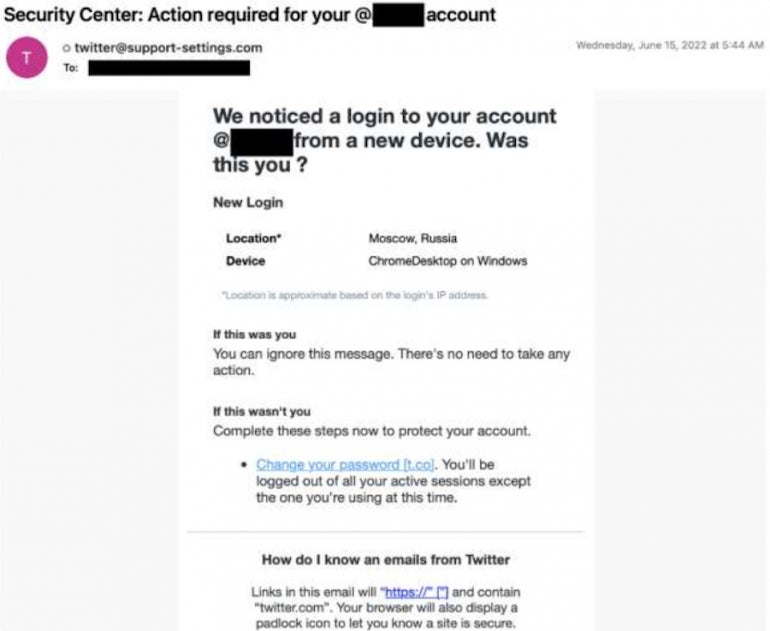
Clicking on the provided link would lead the target to a credential harvesting page impersonating Twitter.
Iran’s TA453, TA456 and TA457
TA453, also known as Charming Kitten, routinely masquerades as journalists from around the world. The threat actor starts benign conversations with its targets, who are mostly academics and policy experts working on Middle Eastern foreign affairs. The conversation usually encourages further dialogue by triggering the interest of the target and showing a knowledge of their work.
Should the victim not answer, TA453 will keep recontacting the target or invite them to a virtual meeting to have further discussions. The goal of the campaign is to obtain the target’s credentials by leading it to a credential harvesting domain controlled by the threat actor.
TortoiseShell, also known as TA456, is another actor from Iran who targets media organizations via other attack campaigns. The threat actor targets users with newsletter emails containing web beacons before compromising these users via malware infection.
TA457 disguises as an iNews reporter to deliver malware to people responsible for public relations in American, Israeli and Saudi Arabian companies. Between September 2021 and March 2022, the threat actor ran attack campaigns approximately every two to three weeks, targeting both generic and individual email addresses at these media organizations.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

