
Some highly skilled cybercriminals have decided to produce different services that they sell to lower-skilled peers. Opening the door for entry-level cybercriminals to successfully run fraudulent operations on the internet and scam people or steal money from them.
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
A lot of products “as a service” have appeared in the cybercriminal underground, so that nowadays almost any person wanting to jump in the cybercriminal wagon might be able to, with the sole condition of having enough initial money to buy such services.
C2 as a service
Cisco Talos published new research about a new platform dubbed “Dark Utilities” by its author. This platform was released in early 2022 and its goal is to provide full-featured command and control (C2) capabilities to cybercriminals for $10.30 (9.99 Euros), which is a very low cost. The platform has enrolled about 3,000 users, which makes approximately $30,951 (30,000 Euros) in income for the people behind the service.
Dark Utilities capabilities
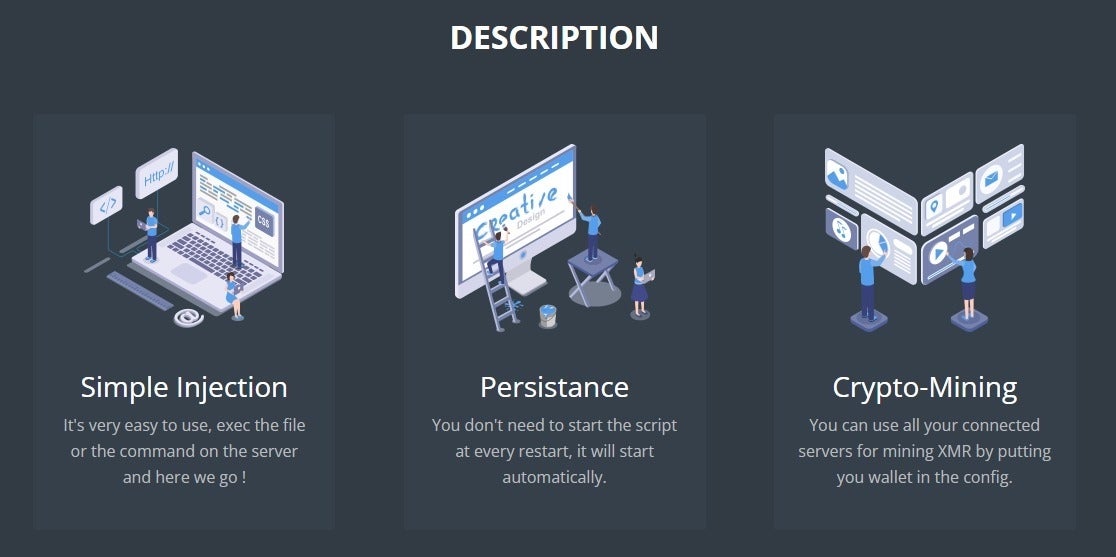
Dark Utilities provides several functionalities (Figure A).
Figure A
Dark Utilities provides code which needs to be executed on a target’s system, which means the attacker needs to have already compromised the system and have access to it. The documentation provided by the platform provides guidance for conducting reconnaissance and identifying/exploiting vulnerabilities to infect servers that can be added to Dark Utilities. Of course, it is possible for an attacker without particular skills to buy compromised systems access from the cybercrime underground and use Dark Utilities with it.
Once executed, the payload registers the service and establishes a C2 communication channel.
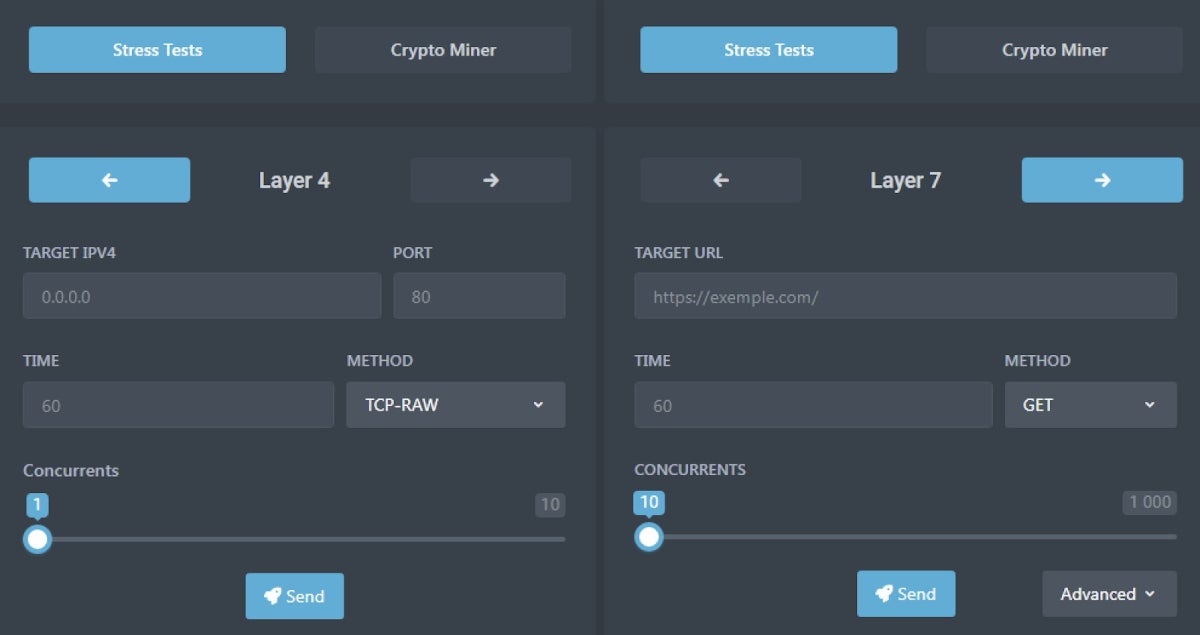
Two types of Distributed Denial of Service (DDoS) attacks are possible using the Dark Utilities: Layer 4, which supports TCP/UDP/ICMP network protocols, as well as some other protocols specifically designed for several gaming platforms such as Teamspeak3, Fivem, Gmod, Valve and some video games.
The Layer 7 type supports GET/POST/HEAD/PATCH/PUT/DELETE/OPTIONS/CONNECT methods (Figure B).
Figure B
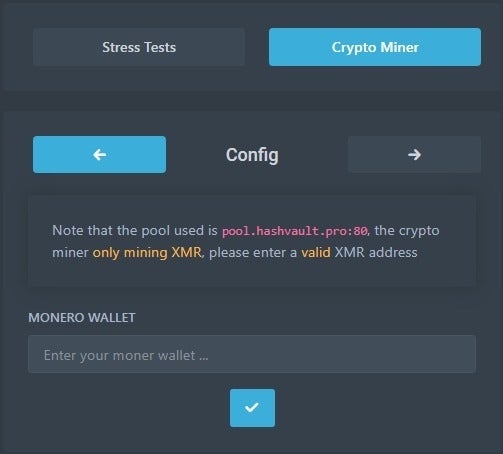
A cryptocurrency mining functionality is also available in Dark Utilities. It is fairly straightforward, as it only allows mining Monero cryptocurrency and only requests the cybercriminals Monero wallet address to work (Figure C).
Figure C
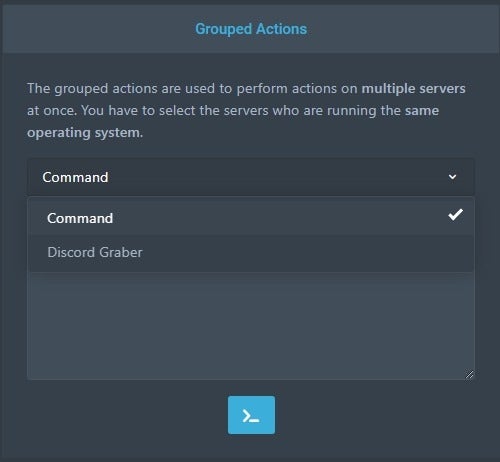
Dark Utilities also provides a way to launch commands on multiple systems in a distributed way, and provides a Discord grabber (Figure D).
Figure D
Dark Utilities panel
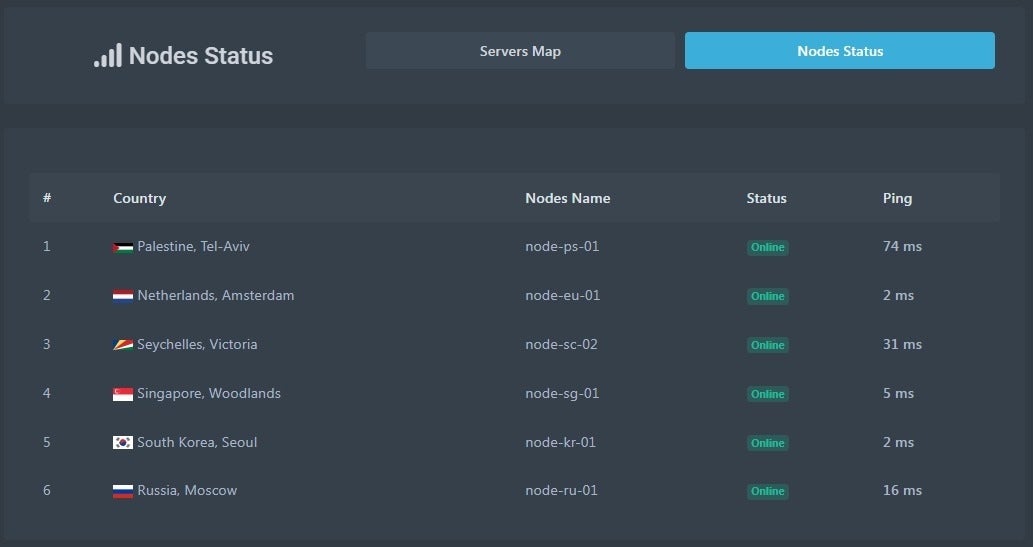
Dark Utilities platform makes heavy use of Discord. It is used for user authentication before providing a dashboard to the user. It shows basic statistics such as server health status and latency (Figure E).
Figure E
A manager administrative panel is also provided to handle all compromised machines belonging to the botnet (Figure F).
Figure F

SEE: Mobile device security policy (TechRepublic Premium)
IPFS payloads
To successfully register a newly compromised machine, a payload needs to be generated and deployed on the victim’s computer.
The current version of Dark Utilities allows attackers to launch payloads on several different operating systems: Linux, Windows and Python-based implementation. The platform also has support for ARM64 and ARMV71 architectures, which they describe as useful for targeting embedded devices such as routers, phones and Internet of Things (IoT) devices.
Yet one of the most advanced aspects of Dark Utilities lies in the hosting of these payloads, as they are actually stored in the InterPlanetary File System (IPFS), which TechRepublic wrote about recently. IPFS is a distributed peer-to-peer network that works without the need to install any client application. IPFS files are accessed via IPFS gateways, and make it really hard to remove data. It is considered “bulletproof hosting”, as the only way to take down that data from the internet is to take it away from every gateway that shares it.
Talos researchers mention that they “have observed adversaries increasingly making use of this infrastructure for payload hosting and retrieval” and it seems skilled cybercriminals will just make more and more use of that technology to store their malicious content, be it phishing pages or malware payloads.
Who is behind Dark Utilities?
Nickname “inplex-sys” appears to handle Dark Utilities, but there is no indication that this persona actually develops the platform. According to Talos, the persona does not have a long history in the cybercriminal underground space, and limits its activities to messaging/bot platforms such as Telegram and Discord. Also, Dark Utilities has been advertised within the Lapsus$ group shortly after its initial release.
The same moniker has also been used in the video game storefront Steam, advertising for Dark Utilities and a few other fraudulent tools aimed at conducting spam attacks on Discord and Twitch platforms or administrate servers.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
How to protect from this threat?
Attackers using Dark Utilities need to find a way to compromise computers on their own. Basic hygiene can prevent compromise:
- Keep the operating systems and software always up to date and patched, in order to avoid falling for common vulnerabilities.
- Deploy security tools on endpoints and servers and have them always up to date.
- Run regular security audits and fix any vulnerability that might emerge from it.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

