Mobile malware is becoming increasingly powerful against banking and financial applications, especially on Android operating systems. Now, research from Cyble reveals that a new version of the Aberebot mobile malware, dubbed Escobar, has been released.
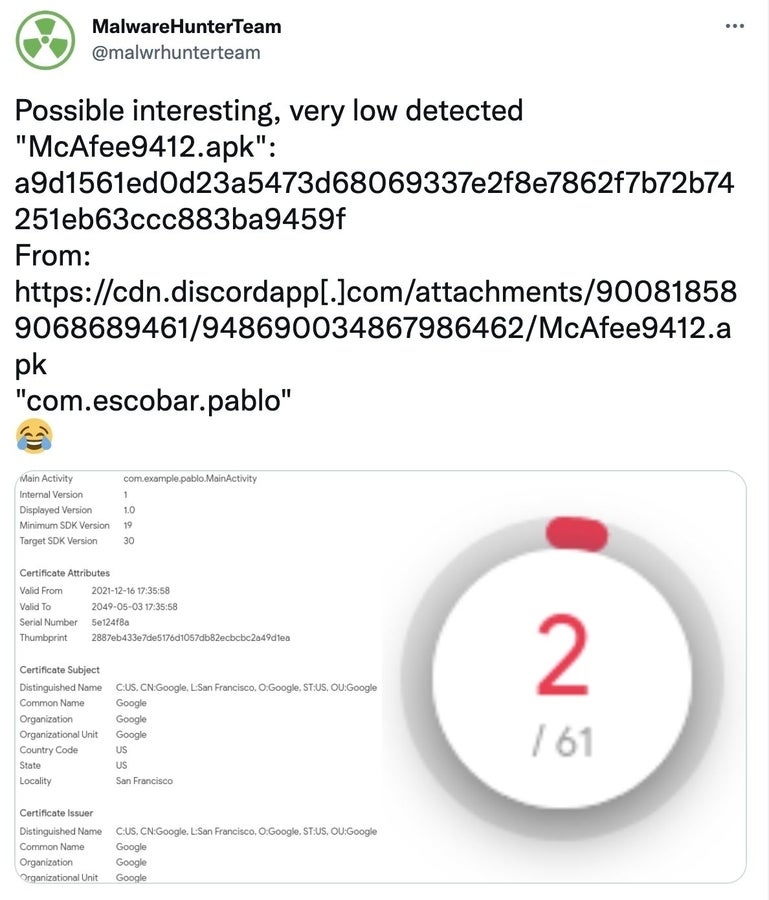
A version of this malware was found in the wild, impersonating McAfee by using the brand in the filename McAfee9412.apk and also using McAfee’s logo as a lure (Figure A). This piece of code can steal nearly everything from the phone it infects, including multi-authentication codes from Google Authenticator.
Figure A
An expensive investment for cybercriminals, or so it seems
Cyble Research Labs exposed an offer from the developer behind Escobar posted in the dark web, showing that it is currently possible to rent it for $3,000 USD per month — and once it will not be beta anymore, it will grow to $5,000 USD per month. The developer insists on the beta aspect and the possibility of bugs, so they’re renting it to only five customers (Figure B).
Figure B
This is an interesting business model, as the developer can have people try, run and use the malware and provide possible bug feedback, while they still make money out of it. Seeing the price for the beta version, one might expect customers of this malware to be experienced cybercriminals who trust their ability to monetize the malware quickly.
The infection vector is not exposed by the developer. Would it be directly available via a legitimate application store, we’d expect the cybercriminal to write about it, since it would raise the value of the malware. Cyble mentions that according to its research, “these types of malware are only distributed via sources other than Google Play Store.”
The previous version of the malware, dubbed Aberebot, first appeared mid-2021 and has already targeted more than 140 financial entities in 18 countries, showing that the development of this malware is active.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
Escobar functionalities
On an interesting note, the developer writes about it: “The malware doesn’t work on Xiaomi MIUI 11 and higher as UI won’t let background services to launch activities (which is how injections work)!”
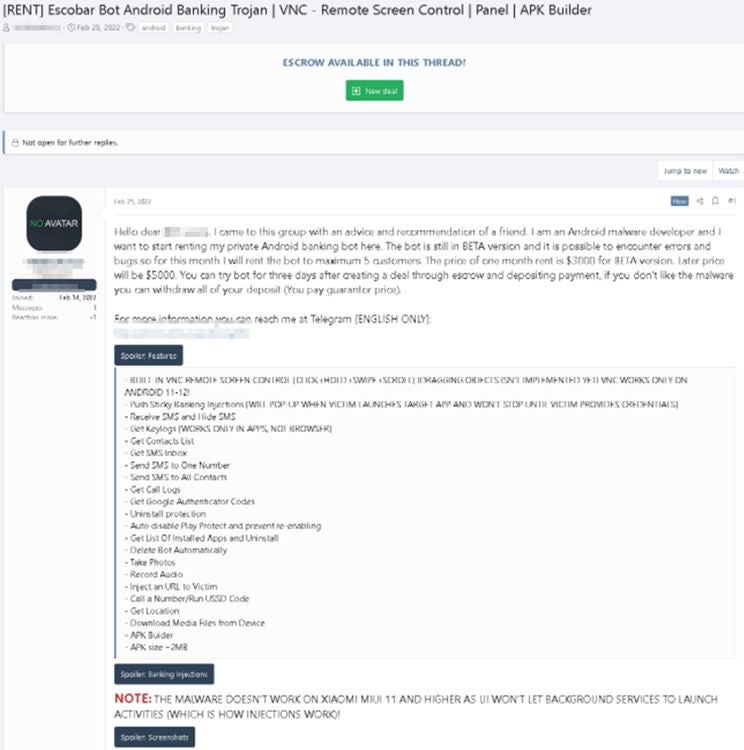
As mentioned, the version of Escobar found in the wild seem to impersonate McAfee (Figure C).
Figure C

The malware needs 25 different permissions from the user, of which it currently abuses 14. It can:
- Collect device location
- Collect contact data (phone numbers, email addresses)
- Collect SMSes
- Send SMSes to a specific phone number or to all the contacts
- Collect call logs
- Steal application key logs
- Steal media files
- Record audio
- Use VNC viewer to remotely control the infected device
- Take pictures
- Inject URLs
- Install/uninstall other apps
- Steal Google Authenticator codes
- Delete itself
All the stolen and collected information is sent directly to a command and control server.
Financially-oriented malware
Like other banking Trojans, Escobar overlays fake login forms on the phone’s screen to trick the user into providing their credentials for e-banking applications or other financially oriented websites.
One particular aspect of this malware that makes it fearsome is that it also steals Google Authenticator codes, which opens new fraud possibilities for the attacker using the malware and makes it possible to bypass 2FA (two-factor authentication).
Should the phone’s user use SMS or Google Authenticator as a 2FA method, the attacker could bypass both.
SEE: Google Chrome: Security and UI tips you need to know (TechRepublic Premium)
How to prevent a malware infection
To protect yourself from mobile malware, it is important to:
- Install comprehensive security applications on your device to protect it.
- Avoid clicking on any link that arrives on your mobile phone, no matter what application it uses, if it comes from an unknown source.
- Avoid unknown application.
- Never download applications from third parties or untrusted sources.
- Check permissions when installing any application. Applications should ask permissions only for necessary APIs. Be extra cautious with applications asking for SMS-handling privileges.
- Be very cautious with applications requesting updates immediately after their installation. An application that is downloaded from the Play Store is supposed to be the latest version. If the app asks for update permission at the first run, immediately after its installation, it is suspicious and might be a sign of malware trying to download more functionalities.
- Enable 2FA. If possible, use Google Authenticator or SMS on another device than the one used for any financial action. That device needs to be safe from malware. This way, even with the stolen credentials in hand, an attacker will not be able to bypass the 2FA request.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.