
Findings in network intelligence firm Gigamon’s Hybrid Cloud Security Survey report suggest there’s a disconnect between perception and reality when it comes to vulnerabilities in the hybrid cloud: 94% of CISOs and other cybersecurity leaders said their tools give them total visibility of their assets and hybrid cloud infrastructure, yet 90% admitted to having been breached in the past 18 months, and over half (56%) fear attacks coming from dark corners of their web enterprises.
The report is an annual survey of more than 1,000 IT and security leaders from across the U.S., EMEA, Singapore and Australia.
Jump to:
- Key to understanding hybrid cloud security
- What is deep observability?
- More cybersecurity collaboration needed to protect hybrid cloud environments
- Education and investment concerns? Not so much
- Zero trust awareness on the rise
- How to close the perception/reality gap
- A checklist manifesto for IT
Key to understanding hybrid cloud security
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
While nearly all respondents (96%) to Gigamon’s poll said cloud security is dependent on gaining visibility across all data in motion, 70% of the CISOs and security operators queried said they lack visibility into encrypted data. One-third of CISOs lack confidence about how their sensitive data is secured.
Chaim Mazal, chief security officer at Gigamon, said most companies exist in the hybrid cloud. “As of today, I would venture to say 90% of the global Fortune 5,000 are operating in hybrid cloud environments,” he said. “They may have started with private clouds first, then the public cloud, then AWS, GCP and/or Azure for different purpose-driven use cases.”
Mazal said the key to understanding what is happening to security across hybrid clouds is deep observability.
“Visibility is a key problem across the board — you can’t secure what you don’t have insights into,” Mazal said. “If you look at the largest causes of breaches, they are systems that have existed for a long time at enterprises that are not part of a monitoring regime. So having end-to-end visibility is something CISOs strive for on a daily basis.”
SEE: Palo Alto Networks’ Ankur Shah on the dangers of a traditional approach to cloud security (TechRepublic)
What is deep observability?
Mazal explained that deep observability, a term coined by Gigamon, denotes network-level intelligence that is immutable: “We take metadata from across network-level environments and route that data into observability tools through smart workflows and routing.”
He added that the web is in the early stages of creating end-to-end visibility, regardless of asset classes.
“With network-level metadata, you get 100% validated data sources that can’t be altered,” Mazal said. “We know that security logs are a great source of data; [however,] they are subject to such exploits as log forging, whereby a nefarious actor tampers with security logs to cover their tracks. With network-level intelligence, you can’t do that because it comprises data validated from beginning to end being fed to your toolsets.”
More cybersecurity collaboration needed to protect hybrid cloud environments
While 97% of respondents said they are able to collaborate across IT teams for vulnerability detection and response, one in six said they do not practice collective accountability because their security operations are siloed. Additionally, the poll suggests CISOs/CIOs aren’t feeling supported in the boardroom: 87% of respondents in the U.S. and 95% in Australia said they are worried their boardrooms still don’t understand the shared responsibility model for the cloud.
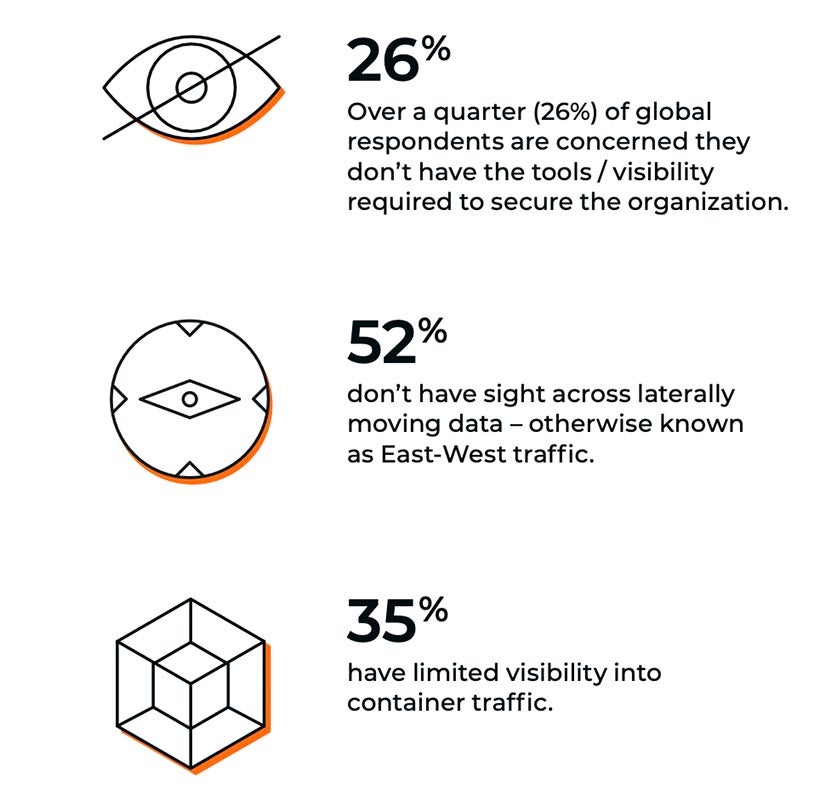
Many respondents said achieving collective accountability is difficult because they can’t see critical data from their cloud environments:
- More than a quarter (26%) of respondents conceded they do not have the right tools or visibility (Figure A).
- 52% said they have no visibility into east-west traffic — network traffic among devices within a specific data center.
- 35% (38% in France and 43% in Singapore) said they have limited visibility into container traffic.
Figure A
In spite of these statistics, 50% of those polled said they are confident they are sufficiently secure across their entire IT infrastructure, from on-premises to the cloud. Mazal said this latter point was surprising.
“Those two things don’t align,” Mazal explained. “Based on the study, there is a false sense of security but, again, we can’t account for those blind spots – being able to solve for them is a key to finding a path forward. Yes, you might have a lot of confidence but not the full picture; if you did, you could go ahead and take appropriate actions and build legitimate confidence. But unfortunately, you don’t know what you don’t know, and sometimes ignorance is bliss.”
SEE: Cybersecurity unaligned with business goals is reactive … and flawed (TechRepublic)
The survey found several points of fear keeping CISOs up at night, with 56% of respondents saying attacks coming from unknown vulnerabilities were top stressors (Figure B).
Figure B

34% of respondents to the Gigamon survey said legislation was a top stressor for them, specifically the EU Cyber Resilience Act. 32% of CISOs said attack complexity was a key fear. One-fifth of respondents said their teams were unable to identify the root causes of breaches.
Additionally, only 24% of global enterprises have banned or are looking into banning ChatGPT, 100% are concerned about TikTok and the metaverse, and 60% have banned the use of WhatsApp due to cybersecurity concerns.
Education and investment concerns? Not so much
What is not worrying security teams is a lack of cyber investment – only 14% of respondents articulated this fear in Gigamon’s survey. In addition, only 19% said security education for staff was critical.
Security leaders in France and Germany, however, bemoaned the scarcity of hybrid cloud cybersecurity skills in their workforces: 23% and 25% of respondents, respectively, said they require more people with these skills. Finally, legislation is a particular issue for leaders in the U.K. and Australia: 41% in the U.K. and 59% in Australia said they were concerned with changes in cyber laws and compliance.
Zero trust awareness on the rise
The zero trust framework, as Deloitte explained in a 2021 white paper, applies across an enterprise’s network and user authentication processes a basic principle of “never trust, always verify.” In Gigamon’s State of Ransomware for 2022 Report, 80% of CISOs/CIOs said zero trust would be a major trend. In this new study, 96% now believe the same for 2023 and beyond. Also, 87% of respondents said zero trust is spoken about openly by their boards, a 29% increase compared to 2022.
“Zero trust is not a product – it’s a methodology,” said Mazal. “For a long time, we didn’t have a clear idea of what that was, but structured outlines by the federal government have given us a good understanding of what that layered approach is today around assets, identity and perimeter, blended in one approach.”
He said network-level insights that are validated across the board and can be fed to IT tools are important pillars. “Immutable data streams across tools is key to zero trust implementation at the enterprise level.”
How to close the perception/reality gap
The Gigamon study’s authors said ensuring data that provides deep observability is fed to traditional security and monitoring tools can help eliminate blind spots and close the gap between what security leaders believe about their organizations’ security postures and reality.
“The first stage to bolstering hybrid cloud security is recognizing that many organizations are suffering from a perception vs. reality gap,” noted the report.
A checklist manifesto for IT
As part of a visibility strategy, IT teams should regularly update network documentation to better administer maintenance, support and security routines. Regular audits garnering information from every node on the network constitute a strong defense against patch and update lapses.
TechRepublic Premium’s network documentation checklist shows how checklists can be integrated with each audit. Available as a PDF and Word document, it will help you document your key assets, from voice equipment to storage infrastructure to battery backups. Learn more about it here.

