
Image: Getty Images/iStockphoto
I want to pose a situation: Say you have users on your internal LAN who need to connect to your servers via SSH, but you also have users on your external WAN who need to do the same. Do you just open up SSH on port 22 and be done with it? Or do you worry that leaving port 22 open on the external side of things might invite attacks?
What if you could open up port 22 for the LAN and port 2222 for the WAN? You can, and I’m going to show you how.
SEE: Windows 10 security: A guide for business leaders (TechRepublic Premium)
What you’ll need
In order to make this work, you’ll need a server that accepts SSH connections and the ability to manipulate the traffic. I’ll be demonstrating on a Ubuntu Server 18.04 instance, which works with Uncomplicated Firewall (UFW). If you are working with a server that doesn’t make use of UFW, you’ll have to modify your firewall rules according to the tool used on your Linux distribution. Also, if you have a network security device that controls the traffic from the LAN and/or WAN, you’ll have to make adjustments there as well–how that is done will depend upon the platform in use.
The machine running SSH will also need to have two network cards, one configured for LAN usage and one configured for WAN usage. For the sake of example, we’ll call those ens5 (LAN) and enp1s0 (WAN).
How to configure SSH
The first thing to be done is the configuration of SSH. This is actually quite simple. Open the necessary configuration file with the command:
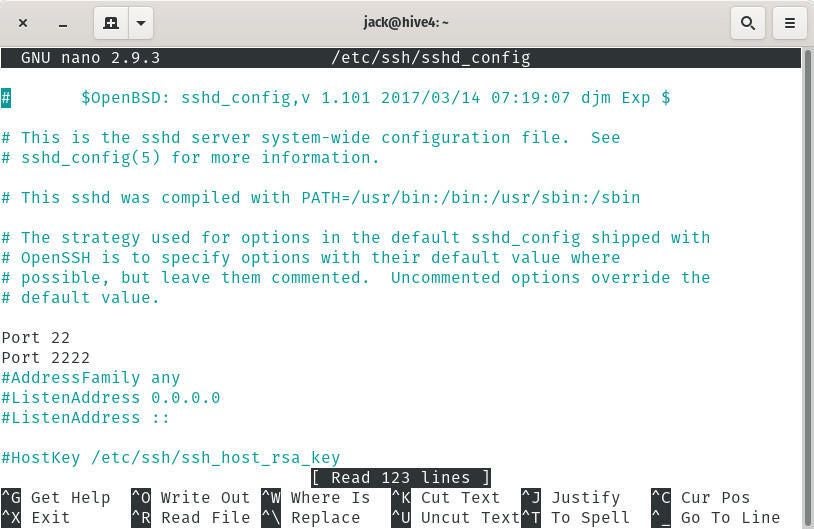
sudo nano /etc/ssh/sshd_config
In that file (Figure A), uncomment the Port 22 line and add a Port 2222 line.
Figure A
Once you’ve made those changes, save and close the file.
Restart SSH with the command:
sudo systemctl restart ssh
Before you continue on, make sure you can SSH into the server using both ports. To connect using port 22, issue the command:
ssh USER@SERVER_IP
Where USER is the remote username and SERVER_IP is the IP address of the server.
You should be allowed in. Once that succeeds, close that connection and test the 2222 port with the command:
ssh USER@SERVER_IP -p 2222
Where USER is the remote username and SERVER_IP is the IP address of the server.
Again, you should be given access to the server.
How to configure the firewall
Now we must configure the firewall to allow SSH connections from the WAN, but only to port 2222. We can do this with the following commands.
First, we block port 22 on the WAN interface with the command:
sudo ufw deny in on enp1s0 to any port 22
Next we allow port 2222 on the WAN interface with the command:
sudo ufw allow in on enp1s0 to any port 2222
Once you have those two rules in place, test the connections from both the LAN and WAN, making sure to use port 2222 on the WAN side connection. You should be allowed in without a problem. If you find this isn’t working, make sure to enable UFW with the command:
sudo ufw enable
And that’s one possible way to specify what SSH connections can be made and from where. Although this is not definitive, as the networking/security hardware you employ might dictate other required measures, it should get you started on the right path.