If you allow Secure Shell (SSH) connections on your Linux servers, you know those servers can be vulnerable to brute force attacks. There are a number of ways you can protect yourself from such attacks. One way is by installing and using the denyhosts tool.
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
Denyhosts is an open source, log-based intrusion prevention security program for servers, which allows you to whitelist servers you never want to be blocked and can even alert you, via email, of any possible intrusion detection.
SEE: Information security policy template download (Tech Pro Research)
I will walk you through the installation and configuration of denyhosts. I’ll demonstrate on Ubuntu Server 18.04, but the process is similar on any supported Linux platform.
Installation
The installation of denyhosts is quite simple. Log into your Ubuntu Server (or open a terminal window) and issue the following command:
sudo apt-get install denyhosts -y
That’s all there is to the installation.
Configuration
The first thing to do is whitelist any machine you want to ensure is never blocked. This is crucial, so you don’t wind up accidentally getting blocked on a valid desktop or server (Don’t skip it). To whitelist a machine, issue the command:
sudo nano /etc/hosts.allow
At the bottom of that file, add any machine for the whitelisting, like so:
sshd: IP_ADDRESS
Where IP_ADDRESS is the address to be whitelisted.
Add as many addresses as you want, one per line. So, if you’re whitelisting a number of hosts, those entries would look like:
sshd: 192.168.1.1
sshd: 192.168.1.10
sshd: 192.168.1.100
Save and close that file.
Now we configure denyhosts, from within the denyhosts.conf file. To do this, open the denyhosts config file with the command:
sudo nano /etc/denyhosts.conf
The first thing to configure (optionally) is the limits for login attempts. You’ll find the following configuration options:
# Block each host after a number of failed login attempts
DENY_THRESHOLD_INVALID = 5
# Block each host after the number of failed attempts exceeds this value
DENY_THRESHOLD_VALID = 10
# Block each attempted failed root login after failed attempts exceed this valueDENY_THRESHOLD_ROOT = 1
# Block each host after the number of failed login attempts (for users found in
# WORK_DIR/restricted-usernames) exceeds this value
DENY_THRESHOLD_RESTRICTED = 1
Although I don’t suggest changing those values, if you have a good reason, go ahead and edit them.
Next, you’ll want to configure the email alert address. In the same configuration file, look for the line:
ADMIN_EMAIL =
Configure the email address you want to receive those alerts. By default, denyhosts uses the local SMTP delivery method (on port 25). If this doesn’t work for you, you can configure the following options (in the denyhosts.conf file) to suit your needs:
SMTP_HOST =
SMTP_PORT =
SMTP_FROM =
Once you’ve configured the necessary outgoing email options, save and close the file.
Restart and enable the denyhosts service with the commands:
sudo systemctl restart denyhosts
sudo systemctl enable denyhosts
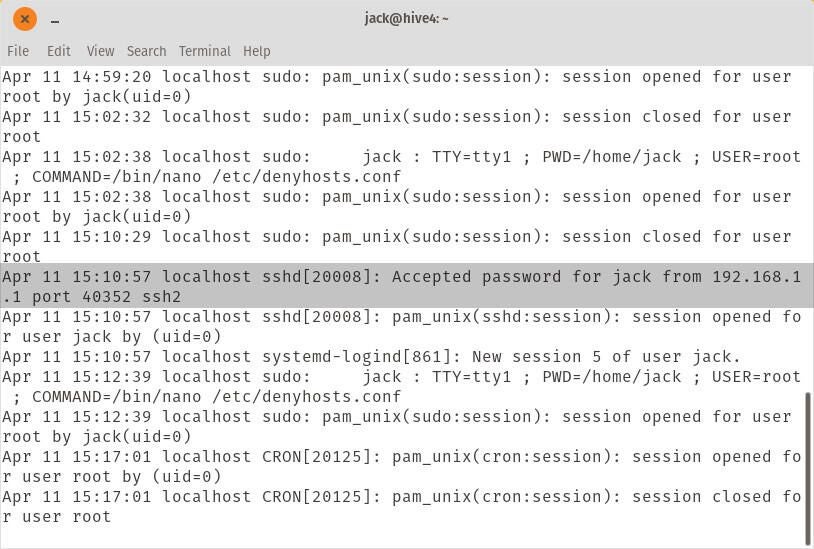
Watching the log file
Out of the box, denyhosts logs to /var/log/auth.log. You can watch that log, in real time, with the command:
tail -f /var/log/auth.log
You will see any successful SSH login attempts listed (Figure A), as well as any attacks (hopefully, you won’t see those).
Testing
The fastest way to test denyhosts is to attempt to log in from another server (one that hasn’t been whitelisted) as the root user. The connection will fail, and the IP address of the offending machine will automatically be added to /etc/hosts.deny. That machine is officially blocked from connecting to the denyhosts-enabled server. Attempt to log in with a valid username, and you won’t be able to connect.
Unblocking
To unblock an IP address, stop the denyhosts service with the command:
sudo systemctl stop denyhosts
You’ll then need to then remove the IP address of the machine you want to unblock from the following locations:
- /etc/hosts.deny
- /var/lib/denyhosts/hosts
- /var/lib/denyhosts/hosts-restricted
- /var/lib/denyhosts/hosts-root
- /var/lib/denyhosts/hosts-valid
- /var/lib/denyhosts/users-hosts
Once you’ve removed that IP address from the above list of files, restart denyhosts with the command:
sudo systemctl start denyhosts
You should be back to working order with the IP address in question. Enjoy your improved SSH security.
