If you administer the Apache web server, you know there are quite a lot of things you can do to help improve its security. For example, you could (and should) employ mod_security. You could also hide directory folders, run only necessary modules, limit large requests, restrict browsing to specific directories, and so much more.
See: How to secure your Apache 2 server in four steps
But there’s two, often-overlooked, steps you can take to help give your Apache server a bit more security: Turning off the Apache signature and configure ServerTokens. Why does this help? Simple. If you broadcast your server’s specific information, you would be informing potential malicious actors what they’re up against. They could know what web server you’re using, what version of the web server, the hosting platform, and even more. You don’t want that information displayed for all to see. So, how do you obfuscate that information? There are two options to be configured, and I’m going to show you exactly how to set them, so to hide away your server details. I’m going to show you how this is done on both Apache (CentOS 7) and Apache2 (Ubuntu). The process is very simple.
What you need to know
We’re going to be dealing with the following two options:
- ServerSignature – used to configure a footer line under the server-generated documents.
- ServerTokens – controls the details which the server sends. The details can include OS and other complied modules.
There are six different ServerToken settings:
- Full (or not specified) – Server: Apache/2.4.18 (UNIX) PHP/7.0.25
- Prod (or ProductOnly) – Server: Apache
- Major – Server: Apache/2
- Minor – Server: Apache/2.4
- Min (or Minimal) – Server: Apache/2.4.18
- OS – Server: Apache/2.4.18 (UNIX)
So the least amount of information you can give out with ServerTokens is Prod, which will only tell the public that the server is Apache. It will not hand out version number, host platform, or any information on modules.
How are these configured?
Apache2 on Ubuntu
Open up a terminal window and issue the command sudo nano /etc/apache2/conf-enabled/security.conf. Within that file, search for SeverTokens and set it to Prod, then search for ServerSignature and set it to Off (Figure A).
Figure A
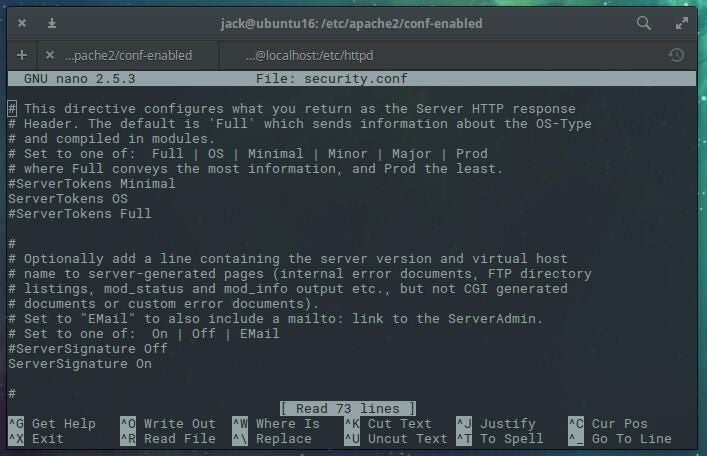
Save and close that file. Restart Apache with the command:
sudo systemctl reload apache2
Apache will now serve up a minimum of information.
Apache on CentOS 7
For CentOS 7, these two directives have to be added (as they are not found in the configuration file by default). Open a terminal window and issue the command sudo nano /etc/httpd/conf/httpd.conf. At the bottom of that file (Figure B), add the following:
ServerTokens Prod
ServerSignature Off
Figure B
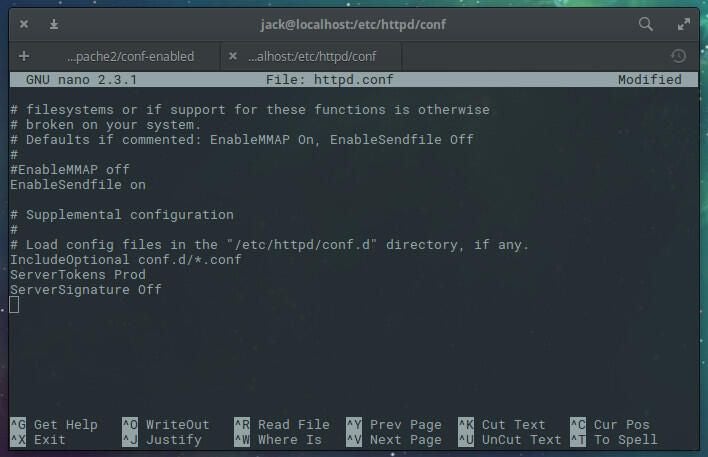
Save and close the file. Restart Apache with the command sudo systemctl reload httpd.
That’s all there is to it
You’ve now configured Apache to announce less information than it was, out of the box. Although this won’t directly harden Apache, it will make it slightly more challenging for hackers to use your web server details against you. Do this for all of your Apache servers and enjoy a bit more security.
