Don’t let mobile malware ruin your day or your device. Be aware of how this threat happens and take good precautions to avoid it.


The phenomenon is not new: cybercriminals use and develop more and more mobile malware. These malicious pieces of code have more and more functionalities and get more dangerous every day. We’ll discuss the evolution of this threat, how it affects companies and how to protect yourself and your company from it.
Mobile malware, as we have covered several times, is a growing trend for cybersecurity. A few days ago, Proofpoint reported a 500% jump in mobile malware delivery attempts in Europe (Figure A).
Figure A
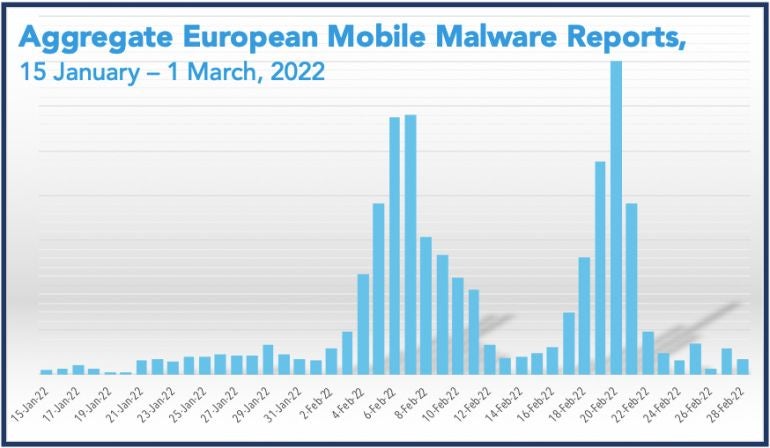
Let’s try to understand why and expose the different threats it represents.
Nearly everyone owns a mobile phone these days, and most people using it are not really aware of the dangers. Also, they generally have less protections on their phones than they have on their computers.
The growth of the mobile market and of the number of applications running on it have become interesting enough for cybercriminals to put more effort on developing malware for phones. Also, more people nowadays use their mobile phones to access a wide variety of services and applications. Those applications might be banking applications or applications that deal with their credit card numbers or just any application that might leak information that can be resold (e.g., credentials for services). This all makes mobile phones really interesting for cybercriminals.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
According to Proofpoint, SMS/mobile messaging campaigns for malware delivery have increased over the past year. The use of SMS and instant messaging makes it possible for cybercriminals to use different social engineering techniques than those used on computers. Loïc Guézo, senior director, Cybersecurity Strategy at Proofpoint, said, “scams, smishing and mobile malware have been increasing exponentially for the past few years. This is a trend that began pre-pandemic and continues. Trust in mobile messaging communications makes it a very attractive platform for commercial and marketing activity; it also makes the mobile channel ripe for fraud and identity theft for cybercriminals.”
Android systems allow their users to get content from multiple application stores. It is also possible to easily install third-party applications from anywhere on the internet. This possibility makes it easier for attackers to infect phones running the Android operating systems.
On the iOS side, the operating system does not natively allow sideloading; it requires jailbreaking the phone, which is not something that the common user will do. This is probably the main obstacle that keep financially oriented attackers from developing and using malware on phones running the iOS operating system.
Mobile malware has evolved from just stealing credentials to far more advanced capabilities.
Some mobile malware types are able to record telephone and non-telephone (via applications) conversations, record audio and video directly from the device or even destroy or wipe the phone’s data.
Also, mobile malware can intercept any interesting information on the phone: credentials for applications, credit card numbers, SMS, and can be even be used for proxying other attacks, which is particularly bad because the phone might be used to target someone else and a legal investigation would probably lead to it, rendering the phone’s user suspect in different cases.
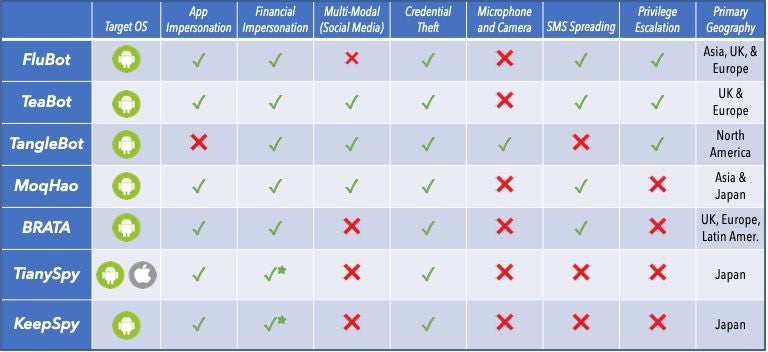
A few of the prominent malware families using SMS as a threat vector, as exposed by Proofpoint, reveal wide targeting and functionalities (Figure B).
Figure B
In addition to mobile malware, smishing attacks is another important threat targeting mobile phone users. Basically, smishing is phishing over SMS. It consists of using SMS to lure victims into an immediate action like clicking a link or downloading a file. As users don’t usually expect to be targeted that way, it has more chances to be opened than a normal phishing on a computer. The phishing scam might then lead to credential theft or malware infection.
To protect from malware threats as well as other mobile threats, it is important to:
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

Cedric Pernet is a senior threat expert with a strong focus on cybercrime and cyberespionage. He currently works at Trend Micro. Prior to that position, he worked for several Computer Emergency Response Teams (CERTs) where he did threat intelligence investigations, incident response, and computer forensics. He was also a Law Enforcement Officer working on Cybercrime in France. He is the author of a paperbook in French language on cyberespionage and an influential person in the cybersecurity community.