
A new report from Trustwave exposes an emerging phishing technique used by cybercriminals to steal credit card data from Internet users.
Initial contact
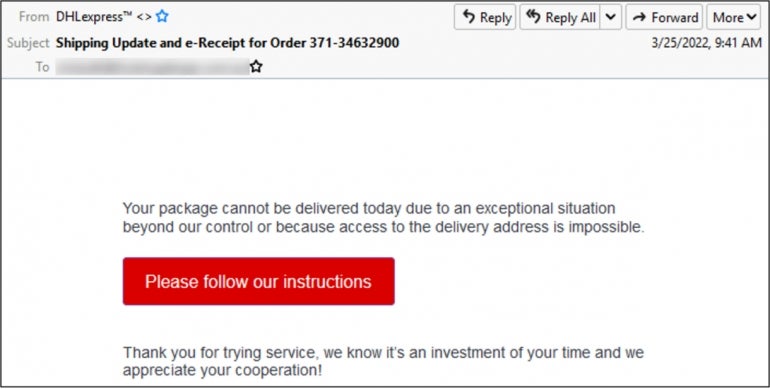
As is often the case, the initial delivery channel for the phishing scam is email. Pretending to originate from DHL, the email content mentions package delivery problems which may be solved by following instructions. The user then needs to click on a link (Figure A).
Figure A
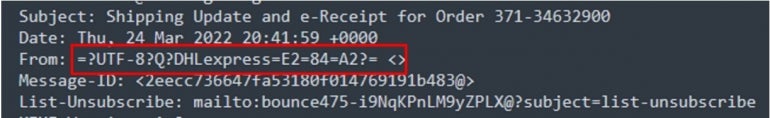
While the email looks legitimate to an untrained eye, a careful examination of the email headers shows that the From field has not been set correctly and does not contain an email address as should be the case (Figure B).
Figure B
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
The clickable link contained in the email will open the user’s browser and direct them to a downloadable PDF file. The PDF shows content seemingly from DHL and tells the user that a delivery has been redirected. To fix the problem, the user must again click on a link.
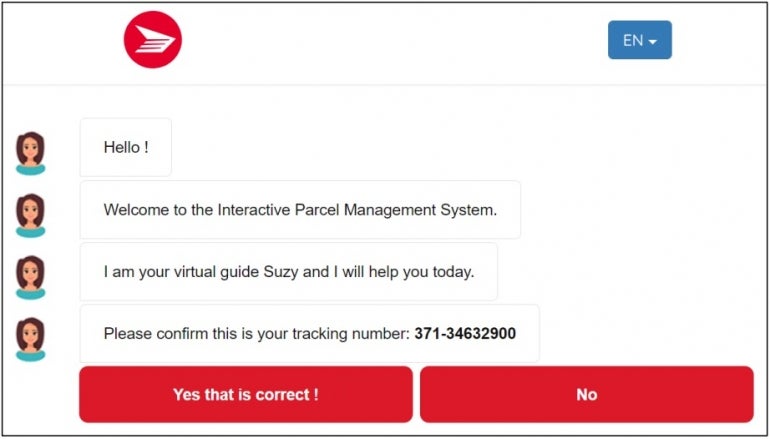
Once the user has clicked, they are led to a chatbot-like page, which is where the real phishing occurs.
The fake chatbot
The page shown to the user at this point is seen as a real chatbot page, but it is not. It is in fact a web page that contains predefined answers offered to the user to solve the package delivery problem.
The user is shown some bot messages asking for confirmation of the package delivery. It is pre-filled so that the user cannot provide any content, but just click on two answers: Yes or No (Figure C).
Figure C
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
Once the Yes option is clicked, the user is then asked if they want the package delivered to their home or office. A picture then shows a damaged package to add legitimacy to the scam.
Finally, the bot tells the user that they need to fill in their delivery details, because DHL only has their name and phone number or email address on file.
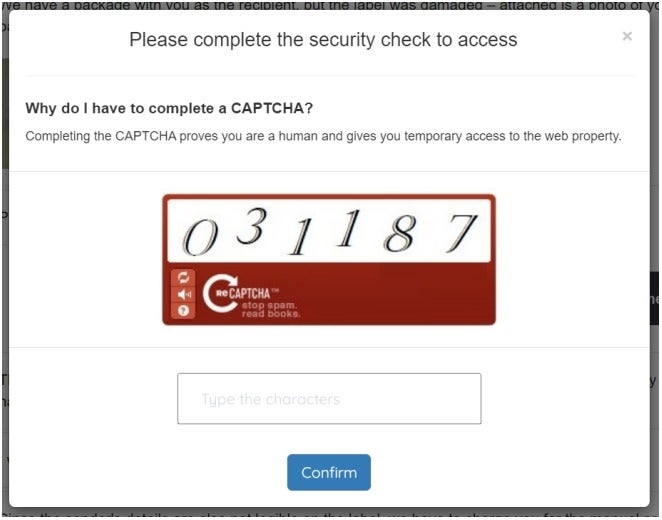
A commonly used method to build trust with victims in a scam consists of multiplying the security measures, to give a false feeling of being completely protected to the victim. This is done at the next step by presenting a captcha to the user. Just like with the chatbot, the captcha is actually only an image and not a real captcha system (Figure D).
Figure D
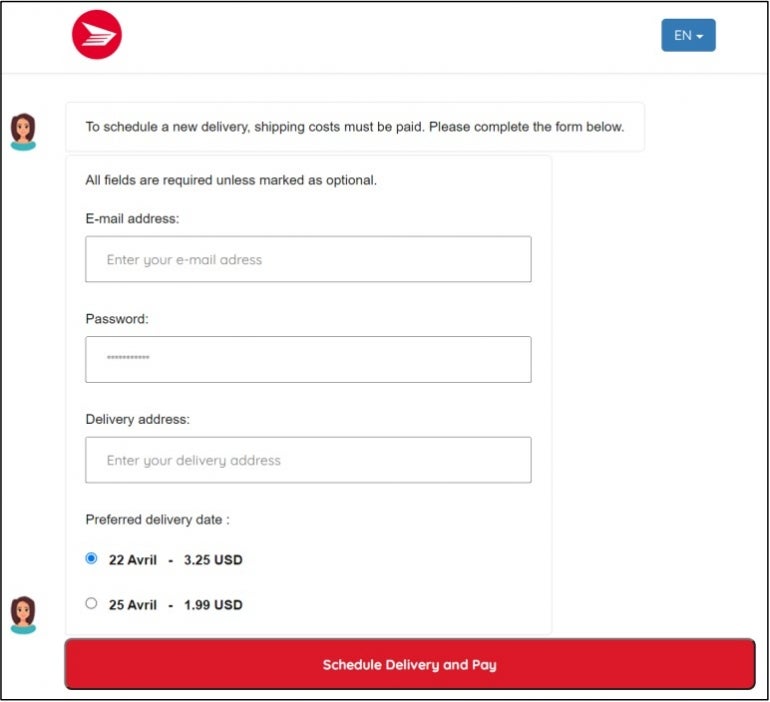
The user is then asked for their email address, password and delivery address. Two different delivery dates are offered to the user with two different small amounts in USD to pay for the delivery (Figure E).
Figure E
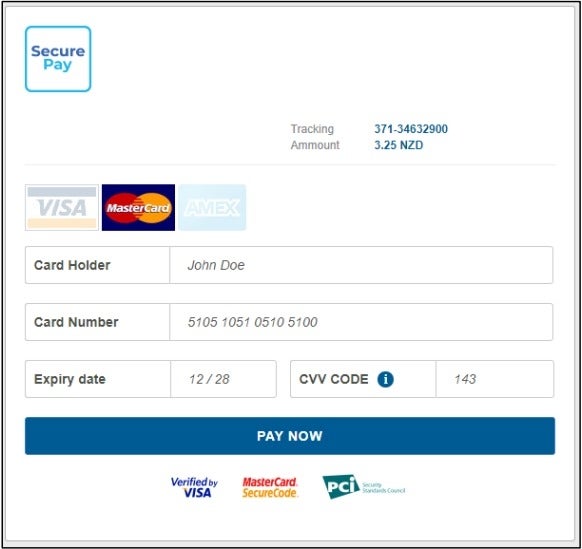
Now that the user has validated a captcha, provided delivery information and possibly provided their email credentials, the final stage of the attack asks the victim to provide their credit card information to pay for the package delivery (Figure F).
Figure F
Once the victim has completed the form, they are shown a final page requesting a security code on their phone (Figure G).
Figure G
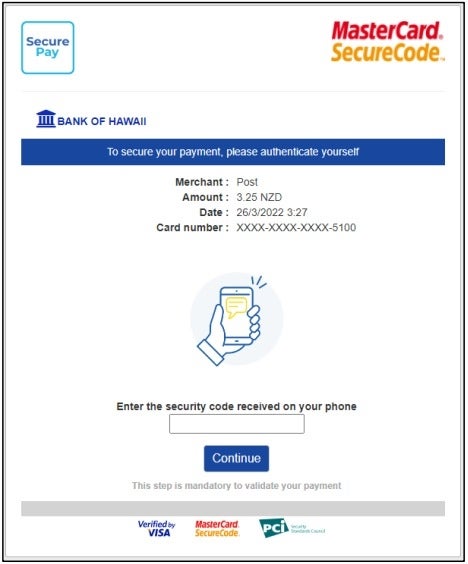
At this point, the victim may notice that they never provided any phone number in this process but may assume that DHL already had it stored.
No code is sent to the phone number and inputting random numbers in the final page redirects to the same page stating the security code is not valid. After five attempts, a confirmation page is shown to affirm the submission was successfully received.
How to protect yourself from this phishing threat
A careful examination of emails should always be done, as they often contain data which might raise alarms. In this case, the From field was badly formatted and easy to spot.
Any suspicious email should be analyzed by a security team before clicking on any link or opening any file.
Email protection solutions should also be deployed in order to detect phishing campaigns and suspicious emails.
The URL the browser is opening should also be carefully checked, as cybercriminals often register fake domain spoofing legitimate brands. In this case, the fraudsters used “dhiparcel” in the domain name. A careful examination would have lead the user to see that it is “DHI” and not “DHL.”
Browser protection solutions should also be deployed in order to detect fraudulent domains.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

