
A new Cybersecurity Advisory has been released by the FBI, the Cybersecurity and Infrastructure Security Agency, and the Department of the Treasury. The advisory describes the recent activities of the Lazarus Group, who specialize in advanced persistent threats and target organizations in the blockchain and cryptocurrency industries.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
Who is the Lazarus Group?
Lazarus Group, also known as APT38, BlueNoroff and Stardust Chollima, is a long-known state-sponsored threat actor from North Korea. The group has been active since 2009. While initially focused on South Korean targets, disrupting and damaging computers from various organizations, the group then began focusing on international financial crime.
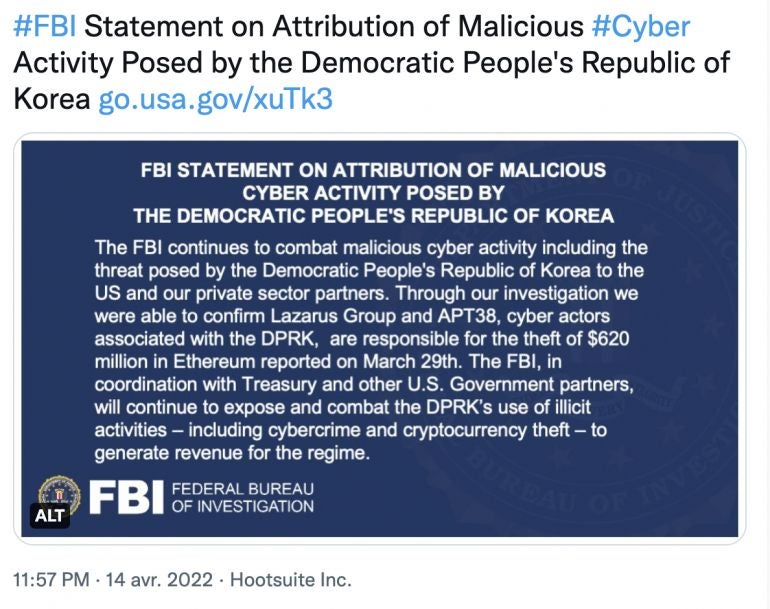
A previous advisory has already been published about cryptocurrency exchanges and financial service companies being targeted by Lazarus. The FBI also announced that Lazarus was responsible for the theft of $620 million worth of Ethereum in March 2022 (Figure A).
Figure A
Initial compromise
The attacks start with spear phishing messages sent on various communication platforms by the group. Those messages are sent to multiple employees within the cryptocurrencies companies, often system administrators, software developers and IT staff.
The messages often promise lucrative job opportunities in order to entice the targeted employee to download malware-laced cryptocurrency applications which the U.S. government refers to as TraderTraitor. Once downloaded and executed, the malicious code installs additional payload.
“This campaign combines multiple popular trends into an attack,” said Tim Erlin, vice president of strategy at Tripwire. “We’ve certainly seen attacks focused on cryptocurrency before, and malicious software isn’t new. It’s important that readers understand that this alert isn’t about a new technology, but increased attack activity. It’s easy to think that you’re not going to fall for a phishing email, but the data shows that malicious emails continue to be successful for attackers. Better to be overly cautious than compromised.”
Payloads
TraderTraitor software is written using JavaScript code with the Node.js runtime environment using the Electron framework. The malicious applications are derived from a variety of open-source projects and pretend to be cryptocurrency trading or price prediction tools. Professional-looking websites are often built by the group to advertise their fraudulent applications (Figure B).
Figure B
The agencies also report that “observed payloads include updated macOS and Windows variants of Manuscrypt, a custom remote access trojan that collects system information and has the ability to execute arbitrary commands and download additional payloads.”
Once the payloads are running, it takes less than a week for the attackers to complete their post-compromise activities, which are tailored specifically to the victims’ environment.
Recommendations
The governmental agencies recommend several measures to mitigate this threat:
- Use network segmentation to separate networks into zones based on roles and requirements.
- Run efficient patch management to avoid being compromised by common vulnerabilities. Prioritize the patching of internet-facing devices.
- Require multi-factor authentication and ensure users change passwords regularly.
- Implement email and domain mitigations to detect newly-registered domains often used by threat actors. HTML protocol should be disabled in emails and email attachments should be scanned for malware.
- Enforce application allowlisting to prevent unauthorized software from being executed.
- Have an incident response plan to respond to cybersecurity threats.
Users should also remain cautious when asked for their recovery phrase. In no circumstance will any company ask for it, as it provides full access to cryptocurrency wallets. Should doubts subsist, the user should reach their IT or cybersecurity department to receive confirmation.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

