
Image: gorodenkoff/Getty Images/iStockphoto
Sometimes, choosing a Linux distribution is a challenge. Given how many options are available, anyone faced with the selection could find their head spinning in a dizzying display of confusion. For certain types of users, the selection gets a bit more focused. A particular type of user is one who either places a higher priority on security and/or those who require a particular security-focused toolkit for their daily job.
Within the world of Linux, there are a few particular distributions that give security considerably more attention. One such distribution is Parrot OS. Before we get into this, know there are two different flavors of Parrot OS—a general desktop distribution (the Home edition) and one purpose-built for security. It’s the latter I want to examine today.
SEE: Security incident response policy (TechRepublic Premium)
What is the Parrot OS Security edition?
Parrot OS Security edition is all about penetration testing and Red Team operations, such as computer forensics, reverse engineering, attack and cloud penetration testing. The security edition of Parrot is geared toward anonymous usage and has a plethora of tools available. All of this is wrapped up in a user-friendly desktop operating system, based on Debian.
Some of the tools you’ll find in Parrot OS Security edition include:
- Anonymous mode start
- I2P
- Two Cents Crypto
- ZuluCrypt
- EtherApe
- Ettercap
- King Phisher
- Tor Browser
- TorChat
- Wireshark
- XHydra
- Zenmap
- debmod builder
- Parrot Cloud Controller
- Spectrum Tool
You’ll find penetration testing tools for:
- Information gathering
- Vulnerability analysis
- Web application analysis
- Exploitation
- Maintaining access
- Post exploitation
- Password attacks
- Wireless testing
- Sniffing & Spoofing
- Digital forensics
- Automotive
- Reverse engineering
- Reporting
Parrot OS Security edition has you covered, regardless of what security issue you’re digging into. Many of these options are command-line tools, so to actually use them, you’ll need to either already be familiar with them, or willing to spend the extra time to get to know them. Of course, anyone looking to make use of such a tool will probably have a pretty good understanding of how it works. If not, you’re in for a pretty steep learning curve.
That’s really where any review of Parrot OS Security edition should start—don’t bother with this Linux distribution unless you know what you’re doing.
Some of these tools could land you in trouble, should you misuse or abuse them. You certainly wouldn’t want to launch, say, aircrack-ng on your company wireless network, unless:
- You know what you’re doing.
- You have already informed those above you of your intention or have permission to do so.
If your focus isn’t security (on a very deep level), Parrot OS Security edition is not for you. If you’re just looking for a distribution that can keep your network activity anonymous, Parrot OS Security edition is not for you.
If you are a security expert, Parrot OS Security edition might be exactly for you.
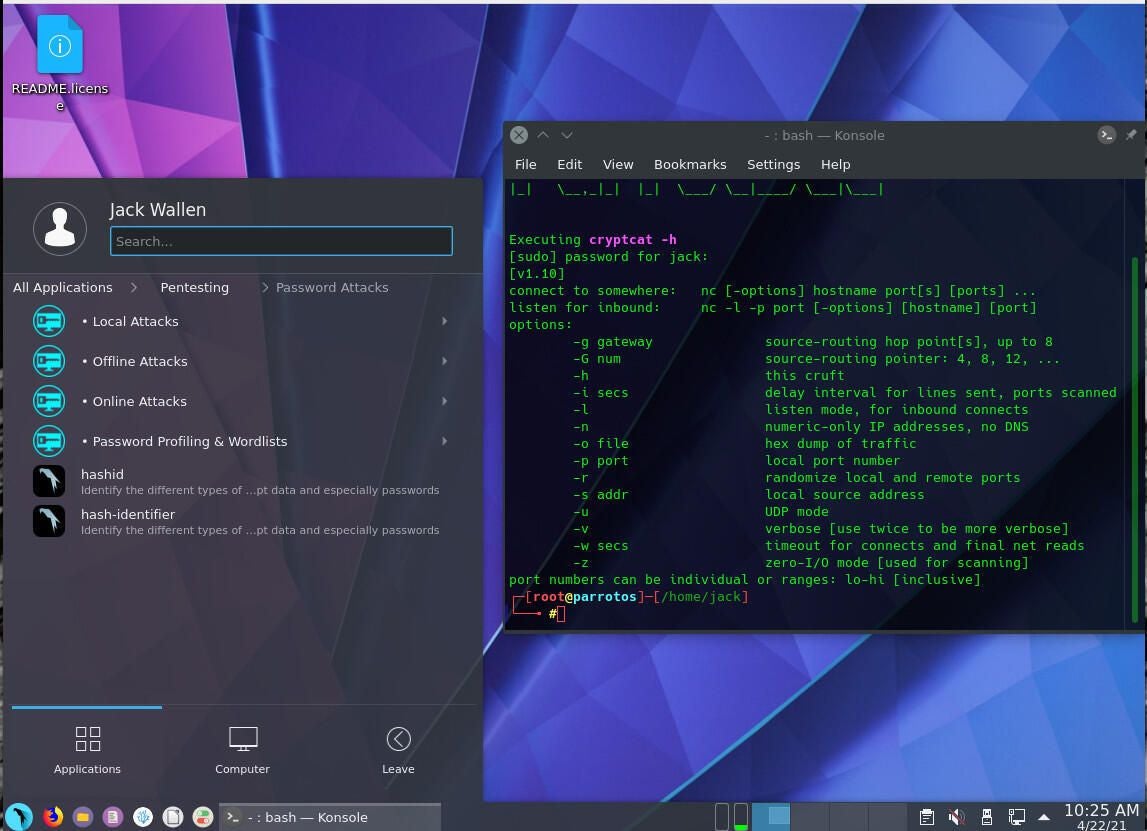
I opted to go with the KDE edition of Parrot OS Security and found the developers have done a great job with the desktop (Figure A).
Figure A
How effective are the tools?
Testing every tool in the Parrot OS Security edition toolkit would take days. Instead, I opted to test some of the tools I was already familiar with. One such tool is the Greenbone vulnerability scanner. Although Greenbone is installed by default, it’s not quite as simple to work with as you might think. You have to launch Greenbone, from the KDE menu, in a specific order:
- Pentesting | Vulnerability Analysis | Openvas – Greenbone | Check Setup Of Greenbone Vulnerability Manager
- Pentesting | Vulnerability Analysis | Openvas – Greenbone | Update New Database
- Pentesting | Vulnerability Analysis | Openvas – Greenbone | Start New Installation
- Pentesting | Vulnerability Analysis | Openvas – Greenbone | Start Greenbone Vulnerability Manager Service
If you don’t run Greenbone in that order, you’ll find it doesn’t work. The Start New Installation Of Greenbone takes considerable time (between 30-60 minutes), so be patient with this. After you complete the above steps, you can start working with the vulnerability scanner (Figure B).
Figure B
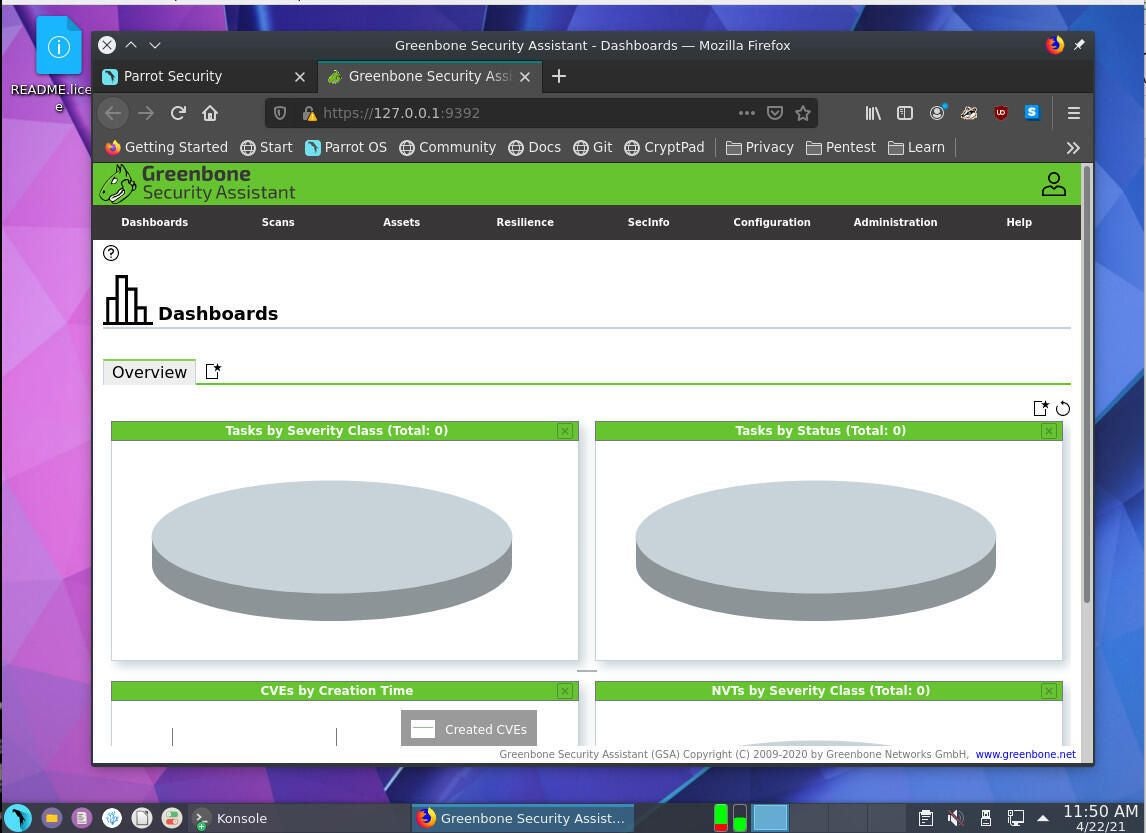
Be sure to check the output of the Start New Installation command, as it will output a random password to be used by the admin user in the web GUI.
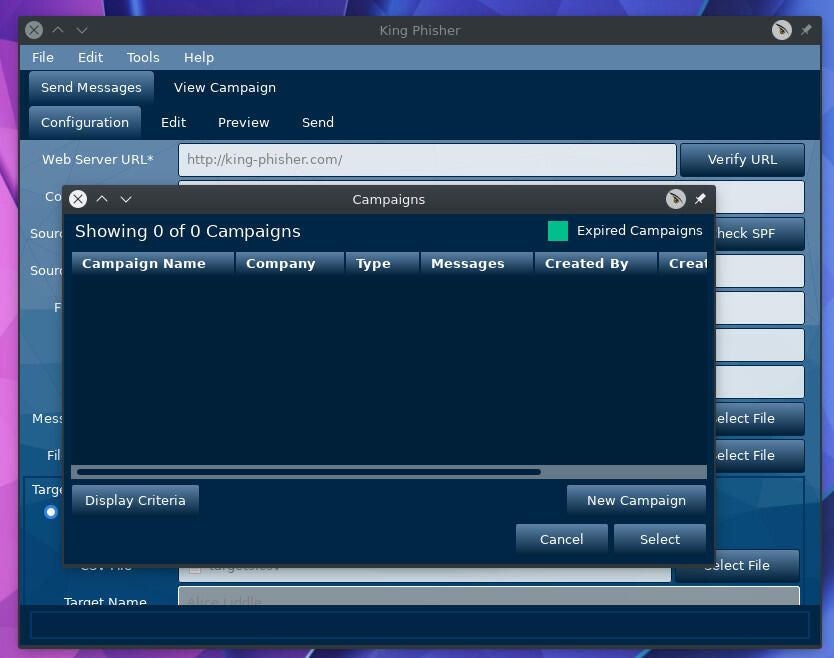
You’ll probably run into a few instances where particular applications either don’t work, or don’t work as you expect them. For example, I attempted to run King Phisher, only to first find out the SSH daemon wasn’t running, and then that it couldn’t connect to the web-based interface. Even the King Phisher service wasn’t running. To use King Phisher, I had to manually start both the services with the commands:
sudo systemctl start ssh
sudo systemctl start king-phisher
Once those commands finished, I could use King Phisher to create a test phishing campaign (Figure C).
Figure C
And that’s how the bulk of these tools will go. You’ll find one you want to try out, only to realize you have some work to do. That’s a key aspect you must consider when working with a distribution like Parrot OS Security edition; it’s going to take time to get up to speed on everything it can do, but the payoff is very much worth the effort.
If you have the time to spend on becoming familiar with the tools found in Parrot OS Security edition, you’ll find this Linux distribution will wind up your go-to for nearly all aspects of digital forensics and penetration/vulnerability testing—that’s how good it is. As long as you know what you’re getting into, this operating system will serve you very well.
Subscribe to TechRepublic’s How To Make Tech Work on YouTube for all the latest tech advice for business pros from Jack Wallen.