Scammers pretend to be highly skilled computer professionals and establish trust with their victim in order to obtain money or installation of fraudulent software.

A technical support scam, sometimes referred to as “tech support scam,” is a kind of online fraud in which a scammer reaches a target, generally by phone, and pretends to offer a technical support service. Using social engineering tricks, the fraudster persuades the target to provide access to his computer via a remote access tool and pretends to fix severe computer problems like dangerous malware infection or data theft. Once done, the fraudster charges the victim for the fake service. This kind of fraud has existed since 2008 but is still very used by groups of scammers.
The most common way to reach users consists of bringing them to a fake website, created by the fraudsters. The fake website shows the user an alert message triggering social engineering tricks to convince the user to call a phone number (Figure A). In addition to the fake pop up message, some scammers websites also use sound alarms or voices to raise the users stress and make him/her call the phone number.
Figure A
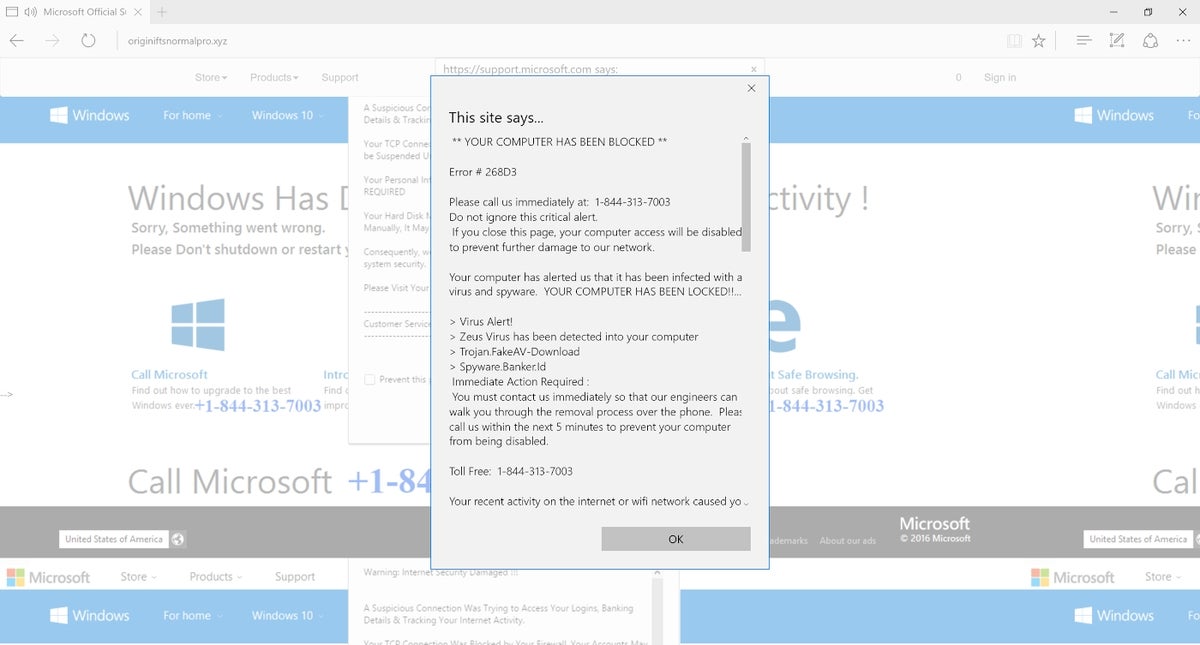
Some tech support scams have also been using email or even SMS messages, but the rate of success of those is significantly lower than alerts shown directly on the user’s screen.
Another technique reported recently by McAfee consists of creating Twitter or other social media accounts pretending to be legitimate technical support websites and using hashtags to be more visible and attract unsuspecting users to their fake websites, which sometimes look very convincing and mimic official websites.
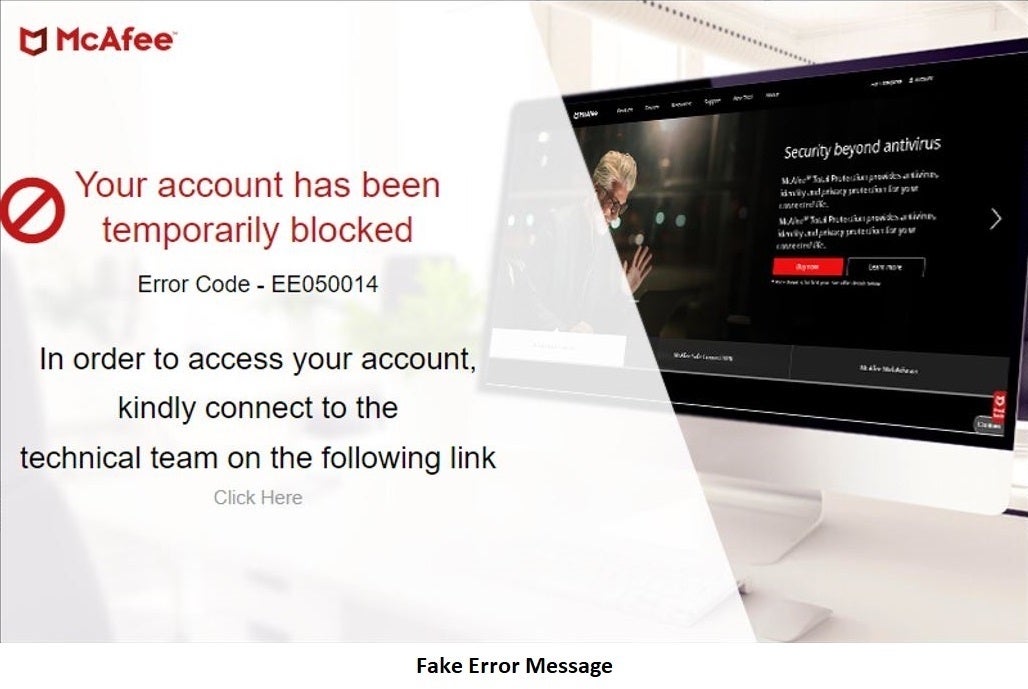
As an example, some fraudulent websites use the McAfee logo or other company logos, inviting users to click on a login or activation link (Figure B). Once clicked, it asks the users for their username, password and phone number. After this step, they show an error hinting the user at calling the technical support service or clicking a link to a chat box to initiate the contact between the scammer and the target.
Figure B
The next step for the scammer consists of managing to get full access to the user’s computer, in order to help him/her.
To achieve this goal, the scammer asks the user to enter a specific URL or to copy/paste it from a chat box into their browser. The link leads to the downloading of a remote access tool that the scammer asks the user to install and run. Once done, the scammer gains access to the computer.
The software used for remote access is generally legitimate software like TeamViewer, LogMeIn, AnyDesk or AweSun.
SEE: Mobile device security policy (TechRepublic Premium)
The scammers often use very technical words, to reinforce the feeling of being professionals and bring the targets to fully believe their every word.
In addition, once they have gained control of the computer, they show the user very graphical interactions which makes users believe they are great professionals and do incredible actions on the computer.
The scammers might use some command line that most users generally don’t understand, like listing directories or type simple commands.
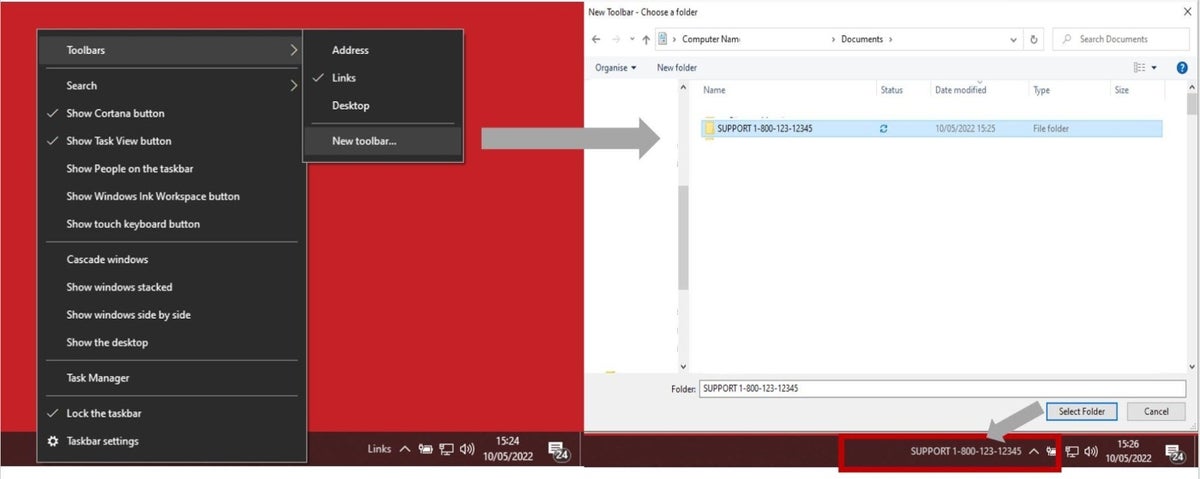
McAfee reports that some scammers also add their phone number in the Windows taskbar (Figure C), which is clever because the users might call them later for another computer problem, real or fake.
Figure C
Some scammers install more software on the victims machine, pretending to install additional security software. That software generally has no other purpose than to make the user believe the computer is being repaired.
They might also install real free security software and make the user believe that it corrected some error.
At this point, the scammer has sufficiently social engineered the victim into believing he/she corrected some major bug or error on the computer.
He will then ask for payment, generally leading the user to a web page to complete a payment by credit card.
Payments amounts vary depending on the scammers. The average amount requested is around $300.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
Generally, tech support scammers are looking for easy money and get it from users paying for their fake computer support.
Yet some scammers also install additional software like cryptocurrency miners, or banking trojan or credential stealing software.
Also, in most cases the user makes the payment while still having the fraudster connected remotely to the computer, as the fraudster helps the user to pay. The fraudster is then in possession of all the credit card information from the user and could possibly use the card information fraudulently, for an additional gain of money.
The scammer might also come back later on the computer, and possibly make new fake errors appear on the user’s screen, and once again make him pay for some technical support services.
For starters, users should never call a number provided by a pop up window. Instead, the user should use the technical support phone number from the security software he uses, or the official technical support line if he is an employee of a company.
Scammers might use fake caller ID to appear like local businesses or trusted companies and phone numbers from such a call should never be trusted.
If you think you have been scammed at some point, immediate measures need to be taken:
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

Cedric Pernet is a senior threat expert with a strong focus on cybercrime and cyberespionage. He currently works at Trend Micro. Prior to that position, he worked for several Computer Emergency Response Teams (CERTs) where he did threat intelligence investigations, incident response, and computer forensics. He was also a Law Enforcement Officer working on Cybercrime in France. He is the author of a paperbook in French language on cyberespionage and an influential person in the cybersecurity community.