
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
Everyone in the IT industry should be aware by now that email is the most used vector for cybercriminals to try to infect employees with malware. Yet, when they are first approached via their website’s contact form, things might look different and fully legitimate, raising a false feeling of security. Here’s how this new social engineering method used to spread the infamous BazarLoader malware, and how to protect yourself from it.
What is BazarLoader and how much of a threat is it?
BazarLoader is a stealth and advanced malware that’s used as a first-stage infector. Once a computer is infected by it, it downloads other malware and runs them. BazarLoader is designed to be very stealth, resilient and has been used in the past for campaigns involving several types of malware like TrickBot, Ryuk ransomware and Conti ransomware, to name a few. It is believed to be developed by the Trickbot gang.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
BazarLoader uses the EmerDNS system, which consists of a blockchain on which domain name records are completely decentralized and uncensorable, which is an aspect Emercoin states clearly (Figure A).
Figure A
This makes the malware very resilient, as no one except the person in possession of the domain’s blockchain private key is able to shut it down.
In addition to being technically very evolved, BazarLoader’s controllers have used innovative ways to spread it and infect users over time. For example, they used emails that contained no links or attached files, pretending to be a company whose free trial service would expire soon and the recipient’s credit card would be charged within a day or two to pay for the subscription. To cancel that payment, the user had to give a phone call to a number that was operated by the fraudsters. They would then provide a link to infect the user. This technique is particularly good for bypassing any threat detection, since no link or file was sent by email. They have also used compromised software installers of VLC and Teamviewer in order to infect their targets.
BazarLoader’s new spreading channel: website contact forms
Abnormal Security recently uncovered a new innovative way from the BazarLoader controllers to spread their malware and infect users.
In this new infecting scheme, the cybercriminals first make initial contact via organizations’ website contact forms. The example provided by Abnormal Security, a cybersecurity company, exposes an attacker pretending to be a Canadian luxury construction company looking for a quote for a product provided by the target.
Once the target answers via email, the attacker establishes his or her cover identity before using social engineering methods to have the victim download a malicious file, which will infect the computer with a BazarLoader malware variant.
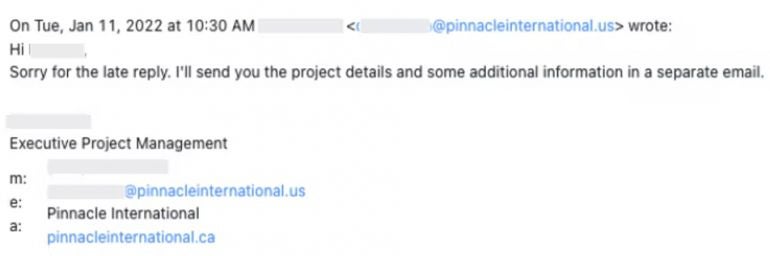
In the example reported by Abnormal Security, a first email reply from the attacker mentions additional information will arrive on a separate mail (Figure B).
Figure B
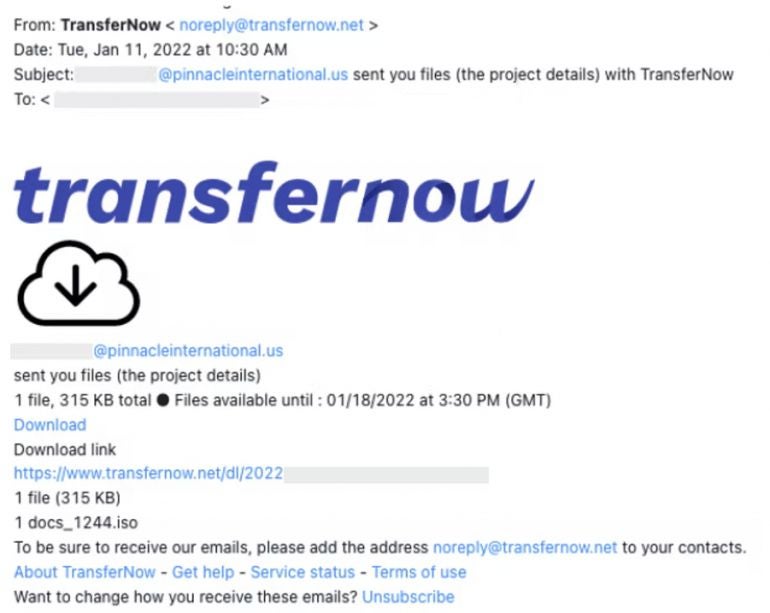
Within a minute, the second email from the attacker lands in the victim’s mailbox, coming from TransferNow or WeTransfer online services (Figure C).
Figure C
The downloaded file is not the usual .exe file or an infecting XLSX or DOCX file one could expect.
The file is a .ISO file with two components. The first one pretends to be a folder but is actually a .LNK shortcut, while the second one is a DLL file pretending to be a .LOG file (Figure D).
Figure D
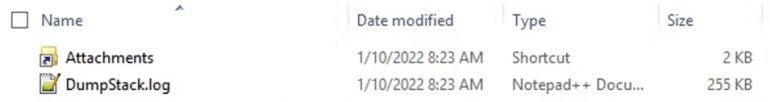
Once the shortcut is clicked, it executes a command line instruction to launch the second file via regsvr32.exe. That second file is a BazarLoader DLL file.
The final step, BazarLoader grabbing another malware and launching it, could not be found by Abormal. However, the sample tried to connect to an IP address which has previously been flagged as spreading ransomware, trojan or bitcoin miner.
How to stay safe from this kind of attack
The attack exposed in this article is based on social engineering, as often. The attacker establishes an initial contact via a contact form, then waits for the target to contact him or her via email and lures the target into opening a file coming from a legitimate online file delivery service. That way, targets might fall into a false feeling of opening a secure file, leading to the infection.
Every file that comes from an unknown source should be carefully handled and not executed immediately. Several steps are useful to determine if the file is safe or not:
- Have the file analyzed by a security product that does more than only signature-based detection for malware.
- If possible, have the file analyzed in a sandbox, in order to have behavioral analysis in addition to static analysis. That analysis should be done by the IT department or by analysts with deep malware knowledge.
- If still in doubt, open the file in a virtual machine with a snapshot system, so that once the file is run and the analysis is done, the virtual machine can be brought back to its pre-launch state.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.

