TENS stands for Trusted End Node Security. TENS is a non-installable, bootable Linux distribution that creates a secure end node from trusted media on almost any Intel-based computer, before booting into the operating system. No hard drive is mounted, no installer is offered. It’s temporary, it’s easy to use, and it turns an untrusted system into a trusted network client.
Must-read security coverage
- UK Police Convicts Pair in £5.5 Billion Bitcoin Launder Case
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- How GitHub Is Securing the Software Supply Chain
- 8 Best Enterprise Password Managers
Before you get too excited, TENS isn’t a pen-testing distro for admins to use to harden their network. TENS is a live desktop Linux distribution that gives the user a level of security they would not have with a standard desktop. That means it’s great to use in places where network security is questionable, or when you need to submit sensitive data, and you don’t trust a standard desktop operating system. In other words, anytime you need to use a network for the transmission of sensitive data, TENS Linux could easily be a top choice for users.
SEE: Securing Linux policy (Tech Pro Research)
TENS was developed by the Air Force Research Laboratory (AFRL) Information Directorate and began as the Anti-Tamper Software Protection Initiative in 2001 (with its flagship products Lightweight Portable Security and Encryption Wizard).
There are three different versions of TENS. Each edition is developed for (and used by) the US Department of Defence, but the developers do provide public versions. The three versions are:
- TENS-Public is a safe, general-purpose solution for using web-based applications and accessing CAC and PIV-enabled web pages. This version of TENS includes a standard and Deluxe version. TENS-Public Deluxe includes the open-source LibreOffice software suite. Both the standard and Deluxe versions are available to download for free on the TENS Download Page. This version of TENS is not intended to be an obfuscation tool, but rather to be a safe operating environment for web-based activity. The Encryption Wizard Public Edition is included in TENS-Public.
- TENS-Professional is similar to TENS-Public but is offered exclusively to non-DoD federal organizations. It is customized by TENS engineers to include specific applications, pre-configured settings for VPN and/or VDI, firewall configuration, web proxy, time zone, desktop background, browser bookmarks, etc. Encryption Wizard Government Edition is included in this build.
- Bootable Media is the secure, DoD version of TENS. Bootable Media has a strong legacy of providing secure remote access to DoD civilian, military, and contractor personnel.
The version of TENS I will demonstrate on is the TENS Public Deluxe edition. As there is no installation available, let’s skip to what this live platform includes.
What you’ll need
The hardware requirements for TENS are pretty small. You’ll need a machine with:
- x86 processor supporting Physical Address Extensions (PAE). Note: The next release of TENS will only support 64-bit hardware.
- 1 GB RAM (1.5 GB for Deluxe).
- Wired, wireless, or cellular broadband tether.
- Ability to boot from either USB or CD/DVD.
- For accessing CAC/PIV-enabled websites you will need a CAC/PIV (TENS office does not provide these) and a USB CCID-compliant smart card reader with updated firmware.
- For printing, either a networked or a local USB-connected printer.
What you can expect
When you boot the live edition (you’ll need to either burn the image to a bootable USB drive or create a virtual machine to use the ISO image) you will be asked to accept the EULA (Figure A).
Figure A
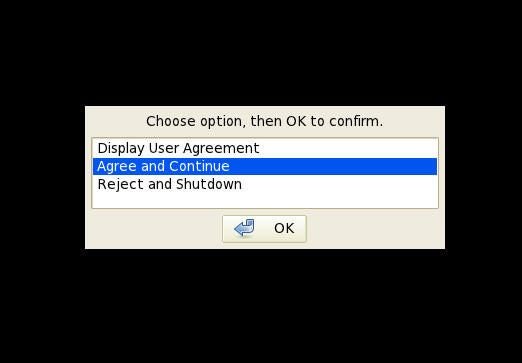
It is highly recommended that you do not use TENS on a virtual machine, as it cannot circumvent vulnerabilities on the host machine. So if you want to get the most out of the TENS security, burn the ISO onto a USB flash drive and boot your machine directly from that.
Select Agree and Continue and click OK.
Shortly after, you will be dumped into the TENS desktop (Figure B).
Figure B
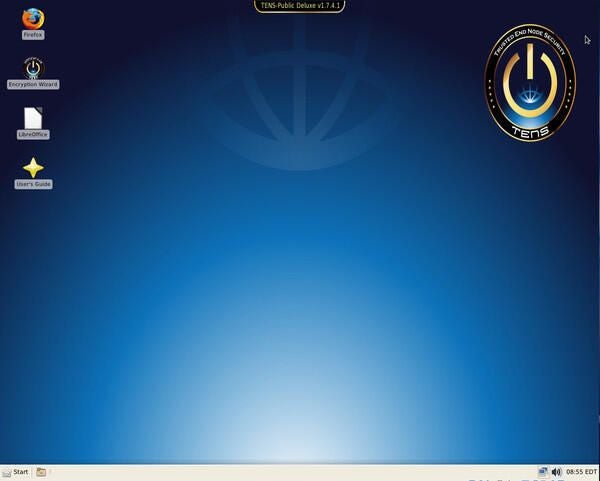
There’s little mystery here. Double-click on either the Firefox or the LibreOffice launcher and start working.
Encryption Wizard
TENS includes an Encryption Wizard, which allows you to encrypt and decrypt files with a user-friendly drag and drop interface. To encrypt a file with this tool, follow these steps:
- Create the file to be encrypted.
- Open the Encryption Wizard.
- Open the file manager from Start | Utilities.
- Locate the file to be encrypted in the file manager.
- Drag and drop the file into the Encryption Wizard.
- Click Encrypt (Figure C).
- Complete the wizard (give the encrypted file a password and fill out metadata for the file).
- When finished, click OK.
Figure C
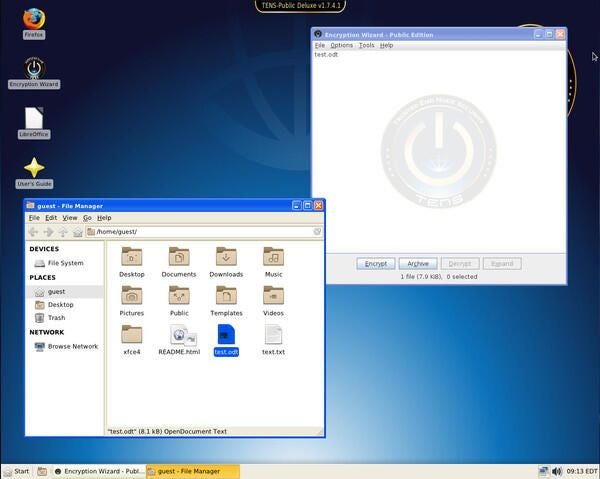
At the end of the wizard, you can decide whether to keep the original file or not. The final encrypted file will end in the .wzd extension and can be sent to anyone with access to the TENS desktop. All the recipient has to do is save the file, drag and drop it into the Encryption Wizard, and provide the necessary encryption password (that you created during encryption). The file will be unencrypted and ready to view.
Security with DNS
Let’s face it, DNS can be insecure. Fortunately, the TENS developers have that covered. If you click on Start | Security, you’ll find two entries:
- Check for OpenDNS
- Enable DNSCrypt
If you want to make use of DNS encryption and OpenDNS for your TENS instance, you must first click Enable DNSCrypt. By doing this, your DNS traffic will be encrypted. You will see no sign that DNSCrypt has been enabled (outside of the Enable DNSCrypt entry changing to Disable DNSCrypt).
Once DNSCrypt has been enabled, click Start | Security | Check for OpenDNS. The check should come up positive, indicating you are now using encrypted DNS over OpenDNS. You should consider this option every time you use TENS.
Security made simple
And that’s pretty much all there is to using TENS. Yes, there is quite a lot going on under the hood of this security-minded Linux distribution, but end users need only worry about what’s happening up top. TENS makes desktop security incredibly simple. Give this live Linux distribution a try and see if it doesn’t become your go-to for when you’d rather not worry about an insecure desktop sending out sensitive information.
