Wireless networks are a two-edged sword. WLANs empower employees and guests, but they also introduce security risks. IT consultant Erik Eckel explains what you need to know to properly configure SonicWALL wireless equipment.

This article is also available as a TechRepublic download.
Wireless
networks are a two-edged sword. WLANs empower employees
and guests, but they also introduce security risks.
While
a wide variety of wireless strategies and devices are implemented, one very
common solution involves deploying SonicWALL
wireless-equipped firewalls. Here’s what you need to know to configure SonicWALL wireless equipment. In
these examples, we’ll use a SonicWALL TZ 170 SP
Wireless model, one of the most frequently encountered
wireless routers in the field, although the steps will also work on other SonicWALL TZ wireless devices.
SonicWALL’s TZ wireless-equipped routers include several features not
found on the non-wireless counterparts. In addition to protecting LANs with
wireless intrusion detection services, which help monitor unauthorized access
and the presence of rogue access points, a separate firewall exists for
securing and separating wireless traffic from the wired LAN.
IPSec encryption and WPA team together to secure wireless communications between
clients and the access point. Guest services can be configured, if desired, as
can HotSpot messaging. Yet another feature SonicWALL wireless-equipped routers possess is distributed
WLAN support for SonicPoint satellite access points.
SonicWALL wireless routers support both the 802.11b and 802.11g
standards. In most installations the SonicWALL device
serves as the access point for the network’s wireless clients. A traditional
UTP cable typically connects the router to the rest of the network.
To
help prevent unauthorized network access, wireless clients must be
authenticated by the SonicWALL’s User Level
Authentication. The devices also support a variety of security protocols,
including WEP, WPA and WPA-EAP.
Selecting
a location for the wireless access point is the first step in configuring a
wireless network. SonicWALL lists several
recommendations for optimizing wireless performance:
Once a
proper location is selected, the next step is to configure the router’s
wireless settings.
As
with other networking services, SonicWALL includes a
wizard to simplify wireless network deployment. To configure a SonicWALL wireless router using the supplied wizard:
|
Figure A |
 |
| Ensure the Enable WLAN checkbox is selected and enter the IP address and subnet mask you wish for the access point to use. |
Once
the wizard completes, you can review the wireless settings by logging on to the
router and clicking the Wireless button. The Status menu will display by
default. It reveals whether the WLAN and WiFiSec
security are enabled, displays channel information and critical IP address
data, among other items. (Figure B)
|
Figure B |
 |
| SonicWALL’s Wireless Status menu displays critical WLAN configuration information. |
To
edit or update the WLAN configuration:
The
device’s WEP/WPA configuration, meanwhile, is administered using the WEP/WPA
Encryption menu. Select the menu from the left navigation bar to change the
authentication type, WEP key mode and change the default key.
From
the SonicWALL’sAdvanced
menu, reached by clicking Advanced from the Wireless sub-navigation menu,
administrators can disable SSID broadcasts, limit the number of maximum client
associations the access point can possess and set the unit’s transmission
strength, among other options. The Restore Default Settings button, found at
the bottom of this menu, supports returning the unit’s wireless settings to
factory presets.
To
introduce additional security, many administrators enable MAC filtering. For SonicWALL TZ
wireless devices you configure MAC filtering by:
|
Figure C |
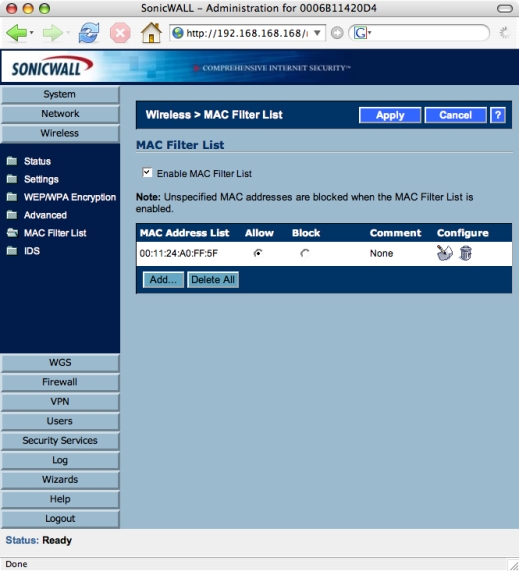 |
| Ensure the Enable MAC Filter List option is checked, and be sure to add authorized systems’ MAC addresses using the provided Add button. Alternatively, you can also block specific MAC addresses using the Block radio button. |
Once
the WLAN is configured, administrators should leverage the SonicWALL’s
intrusion detection capabilities to monitor and protect the wireless network.
Unlike
lower-end devices, SonicWALL wireless-equipped
routers can monitor intrusion attempts and even take steps to respond
appropriately when unauthorized traffic is detected. To configure Wireless
Intrusion Detection:
|
Figure D |
 |
| Wireless Intrusion Detection enables SonicWALL routers to identify, log and dynamically respond to unauthorized wireless traffic. |
The
Enable Client Null Probing feature allows the SonicWALL
device to detect and log Null Probes, such as those triggered by Netstumbler and other programs.
Associate
Flood Detection, meanwhile, monitors for wireless denial of service attacks
that attempt to overwhelm an access point with bogus traffic. Selecting the
Block Station’s MAC Address In Response To An
Association Flood allows the SonicWALL to defend
itself by logging such attacks and dynamically adding the MAC address of the
offending system to its blocked list.
Rogue
Access Point Detection works by scanning for other access points. If other
access points are identified, they’re considered rogue unless they’re
specifically added as authorized access points.
To
enable detection logs, click Log | Categories and check the WLAN IDS box found
within the Log Categories and Alerts section. The subsequent logs should then
be reviewed periodically to ensure unauthorized access attempts are not
succeeding.

Erik Eckel is a managing partner at Louisville Geek and president of Eckel Media Corp. He previously served as Executive Editor at TechRepublic. He received Microsoft Engineer accreditation from Sullivan University and earned his Bachelor's Degree in English from the University of Louisville. He's earned Network+, Windows NT 4.0 MCP+I and MCSE, and Windows 2000 Professional MCP accreditations.