Simultaneous multithreading (SMT) is a common feature found in modern processors, allowing multiple independent threads to execute simultaneously on one CPU core. For x86 processors, the first to feature this ability was the Intel Pentium 4 (“Northwood”) family, released in November 2002. These early CPUs featured two threads on one physical core. For a modern comparison, the Core i7-8809G has four physical cores, each with two threads, for a total of eight logical cores. Intel markets their implementation of SMT as “Hyperthreading.”
Unfortunately, the security implications of having two threads occupy one physical core were not fully considered when this feature was implemented. Two major side-channel exploits discovered in 2018, TLBleed and PortSmash, demonstrate that it is technically feasible for a malicious program running in a single thread in a given physical core to extract data from the other thread in that physical core. Proof-of-concept code of both is available publicly, though as of yet, there is no indication that either have been successfully exploited via drive-by browser attacks.
SEE: Cybersecurity strategy research: Common tactics, issues with implementation, and effectiveness (Tech Pro Research)
Due to the risk that these exploits present, vendors of enterprise-grade laptops such as Lenovo have begun issuing BIOS updates, which allow users the option to disable SMT. These BIOS updates must be applied manually. Lenovo provides a list of products which are susceptible to side-channel exploits, from which users can download the latest BIOS package.
For Windows users, this can be done with an executable. Users of Linux and alternative operating systems can update their BIOS using a bootable CD image. (For ThinkPad models without an integrated optical drive, USB-connected optical drives can be used.) When updating the BIOS for your system, ensure that the system is plugged in to the mains using an AC Adapter, and that the battery charge is full. Do not unplug or turn off your system while the update is being applied.
Disabling SMT on a ThinkPad
Note: This guide was written using a ThinkPad W550s. Although ThinkPads share design cues and firmware to a large extent across the product line, exact steps for your model may vary.
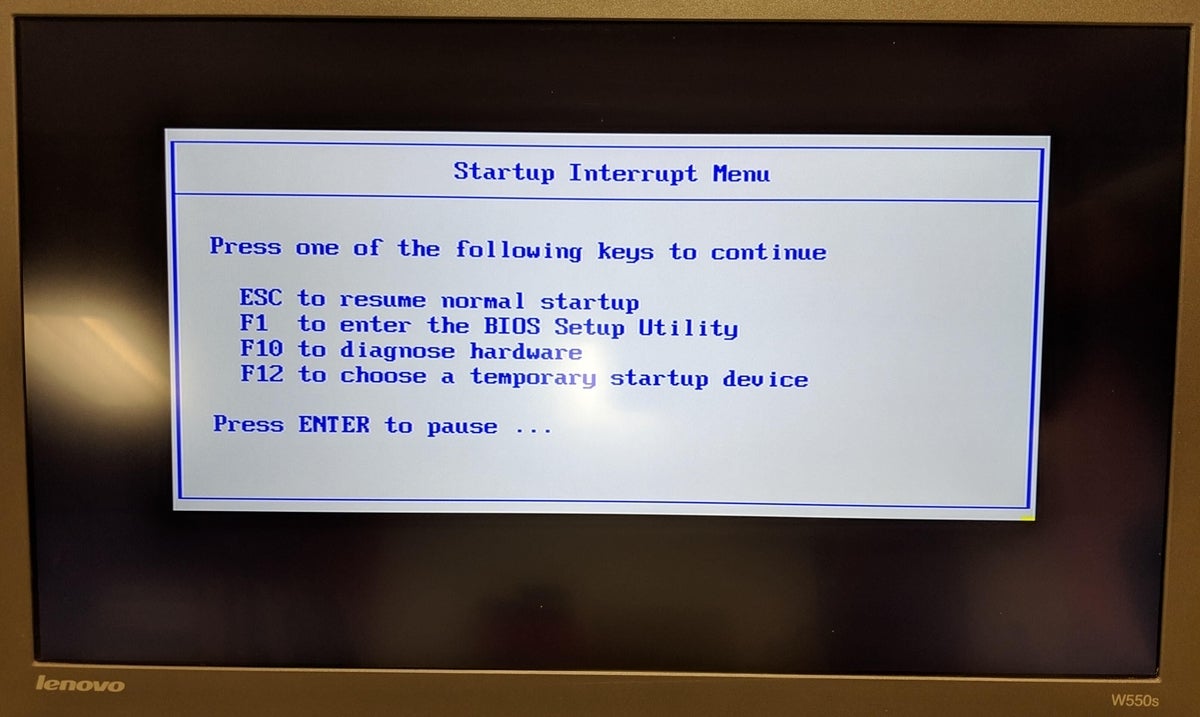
Step 1: When powering on the system, press Enter to access the Startup Interrupt Menu (Figure A).
Figure A
Step 2: Press F1 to enter the BIOS Setup Utility
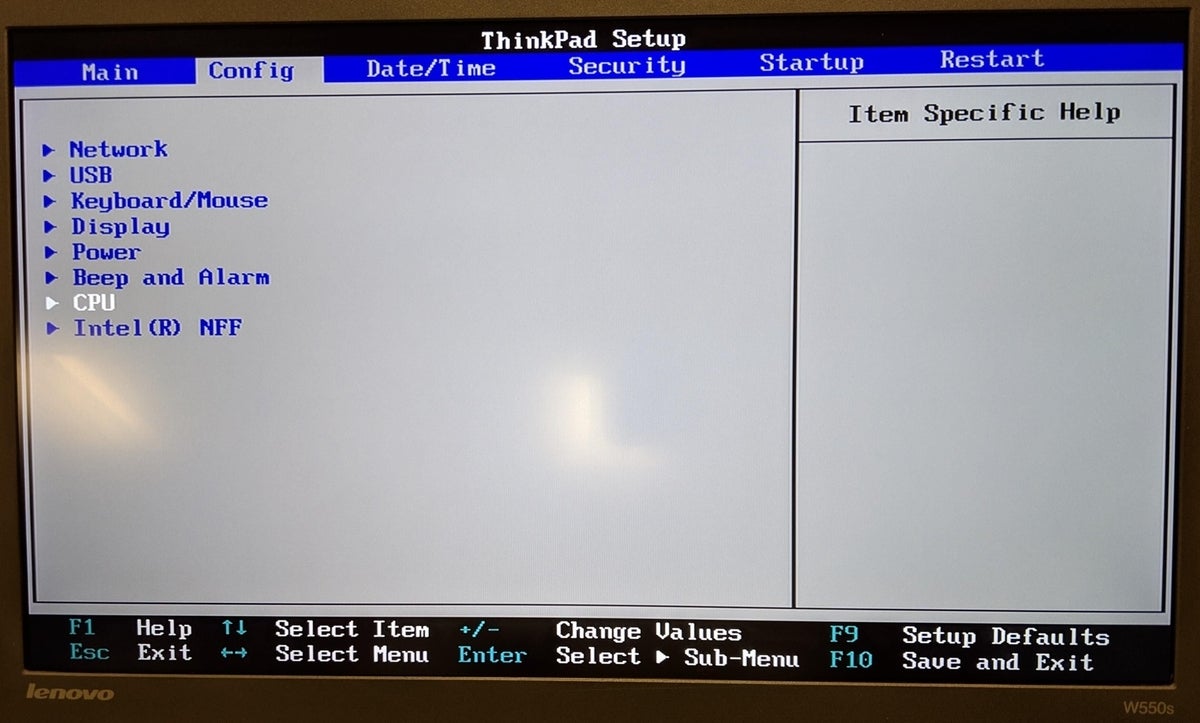
Step 3: Use the left arrow key to select the Config tab. Use the down arrow key to select the CPU option. Press Enter (Figure B).
Figure B
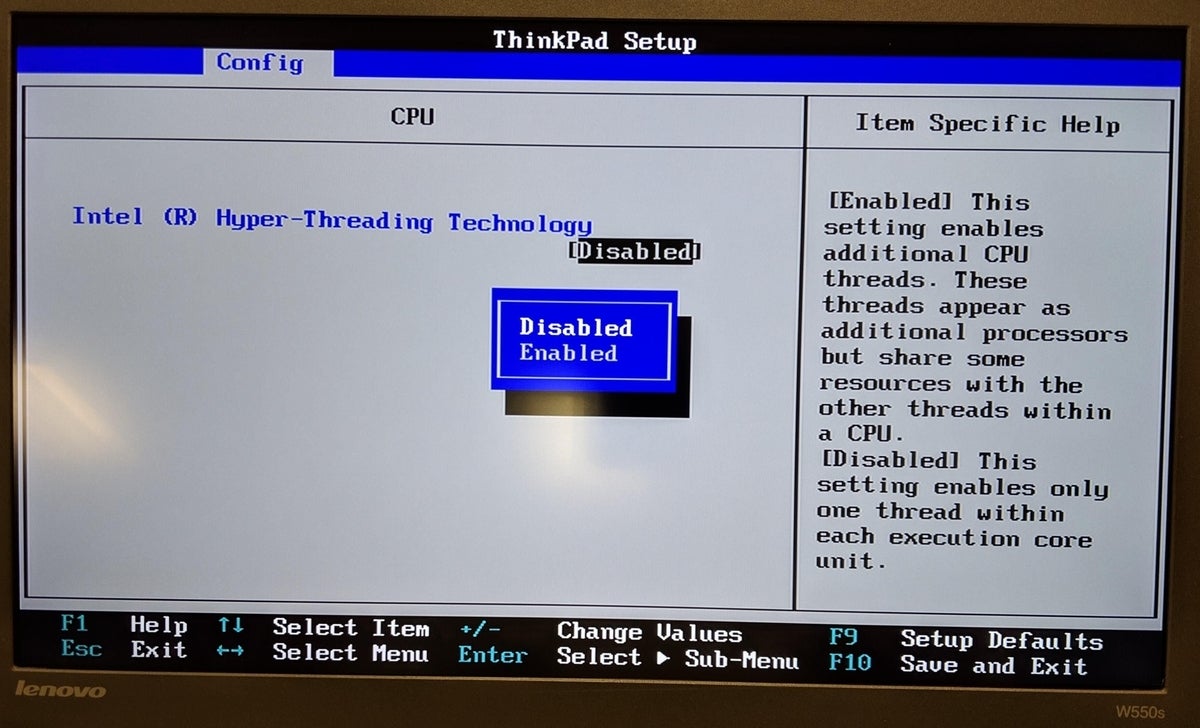
Step 4: For the option Intel ® Hyper-Threading Technology press Enter to open the sub-menu. Use the down arrow to select Disabled and press Enter to select (Figure C).
Figure C
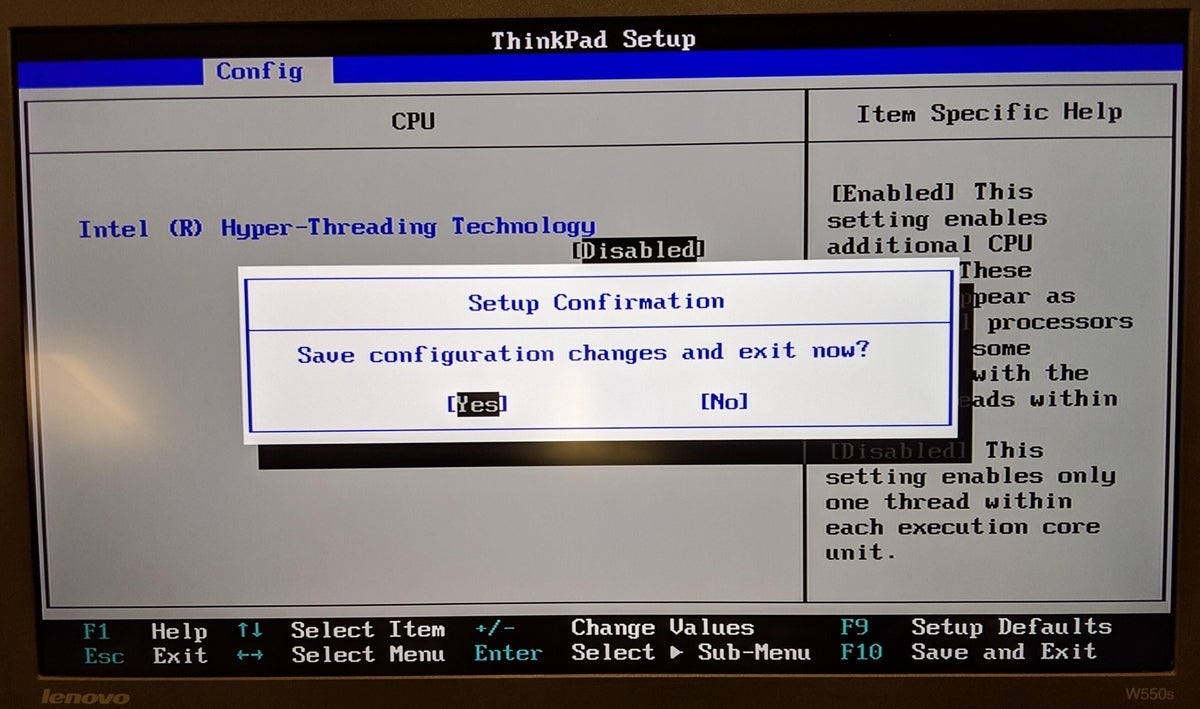
Step 5: Press F10 to save the configuration changes and exit (Figure D).
Figure D
Will disabling SMT decrease performance on my ThinkPad?
It is possible that disabling SMT will decrease performance on your ThinkPad, though this is highly workload dependent. Noticeable performance penalties are possible on programs which were compiled for extensive SMT utilization. Of note, PC gamers often disable SMT on computers to maximize single-thread performance, though this is a very different audience than ThinkPad users.
Because of the security implications of these side-channel attacks, a June 2018 update to OpenBSD disabled SMT at the kernel level. OpenBSD is very security-conscious, and this level of concern may be unwarranted. Ben Gras, one of the researchers who discovered TLBleed, tweeted that “while a cool attack, TLBleed is not the new Spectre.”
Realistically, an outsized amount of risk associated with these side-channel vulnerabilities affects cloud VM providers, as the code executed in VMs is inherently not trustworthy. This is not a concern for end-user workstations at present, as users should only run trustworthy software (or have a group policy to prohibit the execution of unknown software). However, if attackers become capable of exploiting these vulnerabilities through JavaScript, the potential for drive-by attacks makes the risk exposure acceptably high.
Image:
