OneLogin and Okta are two industry-leading identity and access management (IAM) platforms used to secure user access to corporate resources and manage information about user identity. Both products offer similar features and capabilities, but each has unique strengths and weaknesses to consider before purchasing.
OneLogin vs. Okta: Comparison
OneLogin and Okta are enterprise-grade IAM platforms offering security products that customers can mix-and-match to create a customized solution.
| Features | ||
|---|---|---|
| Bundled products | ||
| Single Sign-On (SSO) | ||
| Multi-Factor Authentication (MFA) | ||
| Directory Synchronization | ||
| Identity Lifecycle Management | ||
| Testing Sandbox | ||
| User and Entity Behavior Analytics (UEBA) | ||
| No-Code Automation | ||
| API Access Management | ||
Learn more about IAM in our free PDF: The 10 Universal Truths of Identity and Access Management
OneLogin and Okta pricing
OneLogin offers two bundled plans as well as a la carte pricing. OneLogin’s Advanced plan includes SSO, advanced directory synchronization and MFA for $4 per user per month. The Professional plan adds identity lifecycle management and HR-driven identity management for $8/user/month. Individual workforce IAM features range from $2-$5 per user per month, with the exception of advanced features like the testing sandbox that require a custom sales quote.
Okta’s products are only available individually. The pricing for each feature varies; for example, basic SSO is $2 per user per month, but adaptive SSO is $5 per user per month. Okta has a $1,500 annual contract minimum, with volume discounts for Enterprise clients with more than 5,000 users.
Feature comparison: OneLogin vs. Okta
Single Sign-On (SSO)
Both OneLogin and Okta offer SSO for on-premises and cloud-based applications, as well as endpoint devices like laptops and mobile phones. For an additional $3/user/month, Okta also offers adaptive SSO that analyzes the risk of a login request based on context, such as the device’s location.
Multi-Factor Authentication (MFA)
OneLogin and Okta both have MFA products for enterprise applications, endpoint devices and the cloud. OneLogin’s basic MFA integrates with biometric authenticators (such as Hello World on PCs and Touch ID on Macs) for added protection, whereas Okta offers this functionality as a separate product (SmartFactor Authentication™). Okta’s MFA includes adaptive access policies that assess contextual risk factors like location and user behavior. OneLogin also offers adaptive MFA with machine learning risk analysis, but it’s an additional $5/user/month.
Directory Synchronization
Both OneLogin and Okta offer directory synchronization products that pull in identity and policy information from Active Directory and other sources, providing a centralized control panel to simplify management across the enterprise. OneLogin’s product is called Advanced Directory, and Okta’s is Universal Directory.
Identity Lifecycle Management
OneLogin and Okta both provide identity lifecycle management services that allow you to automatically provision, change and de-provision accounts.
Testing Sandbox
OneLogin has a tool called OneLogin Sandbox that provides a safe staging environment for you to test new IAM features and configurations before deploying them to production. Okta does not offer this feature.
User and Entity Behavior Analytics (UEBA)
Both OneLogin and Okta offer UEBA technology that uses artificial intelligence to analyze account behavior on the network to identify anomalies and threats. OneLogin’s Vigilance AI™ Threat Engine is built into their SmartFactor Authentication product; Okta expects their Identity Threat Protection with Okta AI product to be available in Early Access in the first half of 2024.
No-Code Automation
OneLogin offers multiple avenues for no-code workflow automation: its identity lifecycle management and HR-driven identity products come with built-in automation capabilities, while its Smart Hooks feature allows you to build custom workflows and integrations via APIs. The Okta Workflows product provides a no-code interface to create automated identity-based processes using pre-built templates or custom integrations.
API Access Management
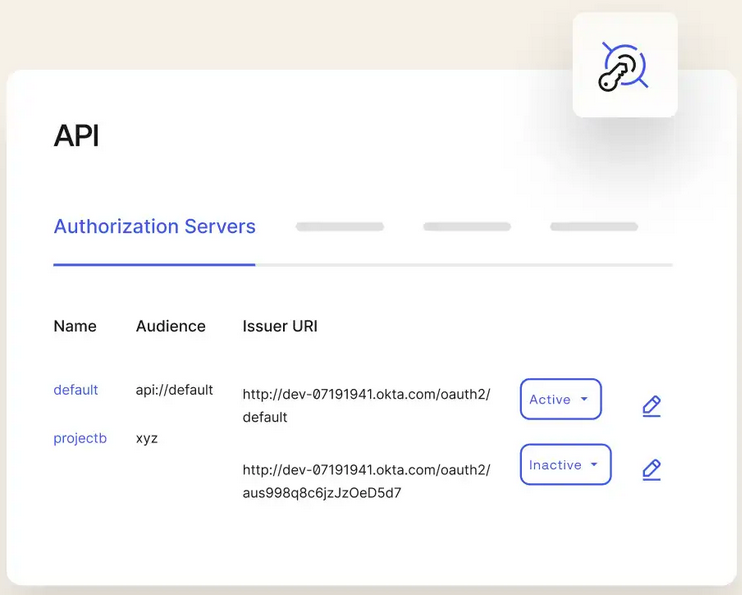
Okta has an API access management tool that streamlines API onboarding, integration and security with a unified, intuitive control panel. OneLogin does not offer API access management functionality.
More cloud security coverage
- Blackpoint Cyber vs. Arctic Wolf: Which MDR Solution is Right for You?
- 6 Best Open Source Password Managers for Windows
- Unified by Design: The Smart Stack Advantage of NinjaOne and Microsoft Intune
- Free Business Email: I Found 8 Legit Ways to Get One
OneLogin pros and cons
Pros of OneLogin
- Provides pricing bundles and a la carte features with no minimums.
- Base product supports biometric integrations and custom workflow automation.
- Offers a testing sandbox to safely validate new features and configurations.
Cons of OneLogin
- Adaptive MFA costs extra.
- Does not provide API access management.
Okta pros and cons
Pros of Okta
- MFA product includes contextual access policies.
- Provides an API access management tool.
- Offers an intuitive no-code identity automation platform.
Cons of Product 2
- Has a $1,500 annual contract minimum.
- UEBA is not available yet.
Methodology
I began my comparison of these two products by thoroughly reviewing the OneLogin and Okta websites to gain a basic understanding of the capabilities and features offered. Then, I downloaded the free trials to evaluate the ease of use of individual features and tools. I also analyzed reviews from Gartner Peer Insights and other trusted sources to learn how real customers use the products and which features factor most heavily into their purchasing decisions.
Download our PDF to learn about The Future of Identity and Access Management.
Should your organization use OneLogin or Okta?
OneLogin and Okta both deliver advanced identity and access management (IAM) capabilities for enterprises. Their individual products have similar pricing, but OneLogin offers bundles and no annual minimums, making it a better option for companies that don’t anticipate spending more than $1,500 per year on their IAM platform. Both platforms offer many of the same features, with some exceptions, such as OneLogin’s testing sandbox and Okta’s API access management tool. Ultimately, the decision will hinge on your organization’s size, requirements and unique security risk profile.

