There are times when you need to remote into a Linux desktop. When that need arises, the most obvious choice of connection is VNC. But what happens when your company (or your home) network doesn’t allow the default VNC port (5901) to remain open? How do you get in?
Fortunately, you have Secure Shell (SSH) to lean on. With this handy networking tool, you can tunnel VNC through SSH, so not only are you not punching through the VNC port, but you’re sending all data through an encrypted tunnel.
It’s actually quite simple to do. You will instruct SSH to create a local tunnel that forwards localhost on port 5901 to a remote machine’s port 5901, only through the default SSH port (22). That, of course, means you must have access to the remote machine, via port 22. If you don’t have access to the remote machine, through SSH, this won’t work.
SEE: Information security policy template download (TechRepublic Premium)
Featured Partners: RMM Software
What you need
Chances are, you have everything you need already installed. This task will require the following:
- Local machine: SSH and a VNC viewer
- Remote machine: Openssh-server and a VNC server (such as TightVNC)
I will assume you already have everything you need installed, and your VNC server is running and accepting connections.
Create the tunnel
The first thing to do is create the tunnel that routes packets from localhost (at port 5901) to the remote host (at port 5901) through port 22. This is done with a single command:
ssh -L 5901:localhost:5901 REMOTE_IP
Where REMOTE_IP is the IP address of the remote host.
If you’ve never SSH’d to this remote host, you will be asked if you want to add the remote host to your local ~/.ssh/known_hosts file (Figure A).
Figure A
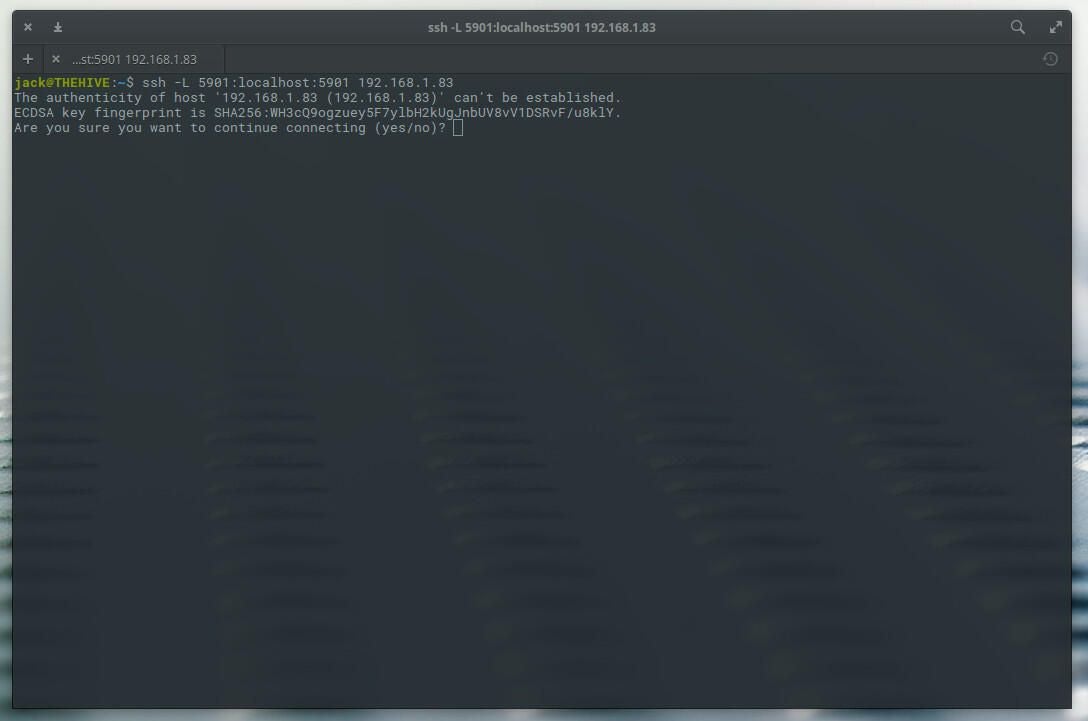
Type yes and hit Enter on your keyboard. You will then be prompted for the remote user’s password. This will assume you have the same username on both local and remote machines. If you do not, you can always add the remote username like so:
ssh -L 5901:localhost:5901 USER@REMOTE_IP
Where USER is the remote username and REMOTE_IP is the remote IP address.
Note: For an even more secure connection, I suggest you make use of SSH Key Authentication. (See: How to set up ssh key authentication.)
Connecting your VNC Client
Now you need to fire up your VNC client. It won’t matter what client you use. What does matter, however, is the address you use to make the connection. Instead of entering, say, 192.168.1.83:5901 for the remote address, enter localhost:5901. Why? Because we’ve created an SSH tunnel from localhost:5901 to REMOTE_IP:5901 (where REMOTE_IP is the IP address of the remote machine). Once you click connect, your VNC client will use the encrypted SSH tunnel and make the connection between local and remote machines on port 5901. You should then be able to work on the remote desktop, using VNC, thanks to SSH.
Not only is your VNC connection good to go, but it’s also more secure than if you had simply used the default VNC port. Enjoy tunnelling VNC through SSH.



